Microsoft's November 2019 Patch Tuesday: Tenable 電子報

With over 70 CVEs, Microsoft’s November 2019 Patch Tuesday corrects 13 critical vulnerabilities, including a patch for an Internet Explorer vulnerability exploited in the wild.
Microsoft’s November 2019 Patch Tuesday contains updates for 74 CVEs, 13 of which are rated critical. This month’s release covers 16 remote code execution (RCE) vulnerabilities and 27 elevation of privilege (EoP) flaws across a variety of products. Additionally, Microsoft has patched an increased number of vulnerabilities in Hyper-V, a number of which were denial of service (DoS) flaws. The following is a breakdown of the most important CVEs from this month’s release.
CVE-2019-1429 | Scripting Engine Memory Corruption Vulnerability
CVE-2019-1429 is a critical flaw in Internet Explorer, which Microsoft notes as being exploited in the wild. This RCE exists due to a flaw in the way the scripting engine handles objects in memory in Internet Explorer. An attacker who is able to exploit this vulnerability could gain the same rights as the current user. Exploitation is somewhat mitigated in that an attacker would need to entice a user to visit a crafted web site or embed an ActiveX control marked "safe for initialization" in an application or Microsoft Office document.
CVE-2019-0721, CVE-2019-1397, CVE-2019-1398, CVE-2019-1399 | Hyper-V Remote Code Execution Vulnerabilities
CVE-2019-0721, CVE-2019-1397, CVE-2019-1398, and CVE-2019-1399 are RCE vulnerabilities in Windows Hyper-V. An attacker could run malicious code on a guest operating system that could cause the Windows Hyper-V host to execute arbitrary code. An attacker would need to gain access to a virtual machine (VM) through other means on the vulnerable host, but once access is obtained, an attacker could escape the VM sandbox and pivot to other VMs on the same host.
CVE-2019-1457 | Microsoft Office Excel Security Feature Bypass
CVE-2019-1457 is a security feature bypass vulnerability in Microsoft Office for Mac caused by a failure to enforce macro settings in an Excel document. This flaw was publicly disclosed on October 30 by Outflank, an IT Security firm focused on red teaming and security testing. The Outflank blog post details attack scenarios using the SYLK file format to include XLM macros into SYLK files. Because SYLK files do not open in Protected View, an end-user opening a specially crafted file would receive no warning or prompt from Excel about opening the file and would have none of the protection offered by the Protected View security feature. Additionally, if Office for Mac has been configured to use the “Disable all macros without notification” feature, XLM macros in SYLK files can be executed without prompting the user, thereby allowing a remote attacker to execute arbitrary code with the privileges of the user opening the specially crafted file.
CVE-2019-0712, CVE-2019-1310, CVE-2019-1309, CVE-2019-1399, and CVE-2019-1399 | Hyper-V Denial of Service Vulnerabilities
CVE-2019-0712, CVE-2019-1310, CVE-2019-1309, and CVE-2019-1399 are denial of service (DoS) vulnerabilities within Windows Hyper-V. An attacker who has the toolsets to exploit this vulnerability could consume the resources of a target server and cause it to crash. Attackers need a privileged account on the guest operating system, running as a VM to exploit this vulnerability.
CVE-2019-16863 | Microsoft Guidance for Vulnerability in Trusted Platform Module (TPM)
As part of the November updates, Microsoft released the security advisory ADV190024 to discuss CVE-2019-16863. In certain Trusted Platform Module (TPM) chipsets, a vulnerability exists which weakens key confidentiality protection for the Elliptic Curve Digital Signature Algorithm (ECDSA). While this flaw is not in Windows and does not exist in a specific application, it was important enough that Microsoft released this advisory. Administrators are encouraged to contact their TPM manufacturer for firmware updates as well as verify additional mitigation steps that may be required beyond a firmware update. At the time this blog was published, Microsoft notes that there does not appear to be any evidence of an exploit in the wild and that the issue was reported through coordinated disclosure.
Tenable 解決方案
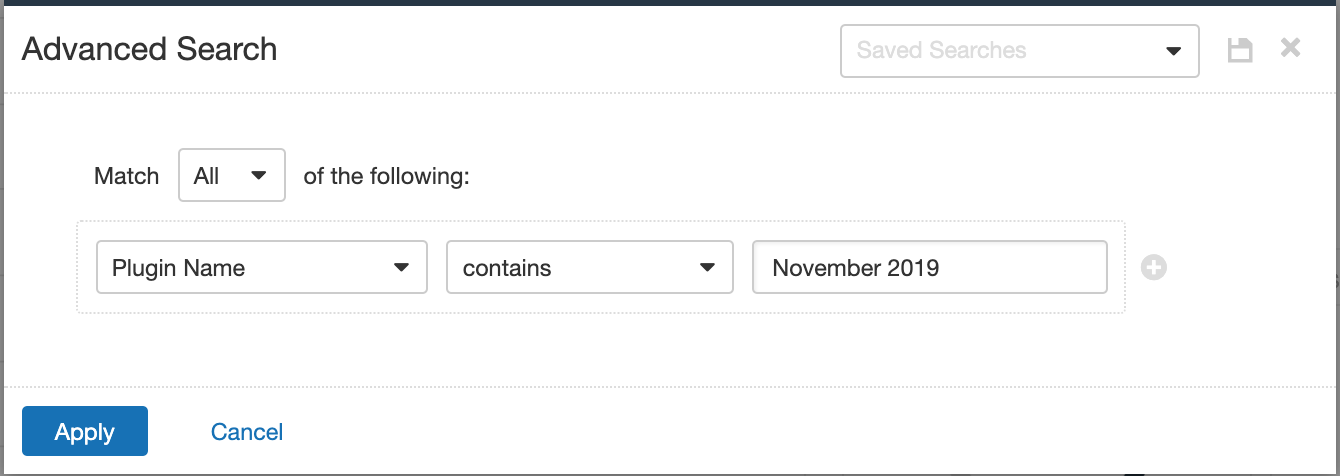
Users can create scans that focus specifically on our Patch Tuesday plugins. From a new advanced scan, in the plugins tab, set an advanced filter for Plugin Name Contains November 2019.
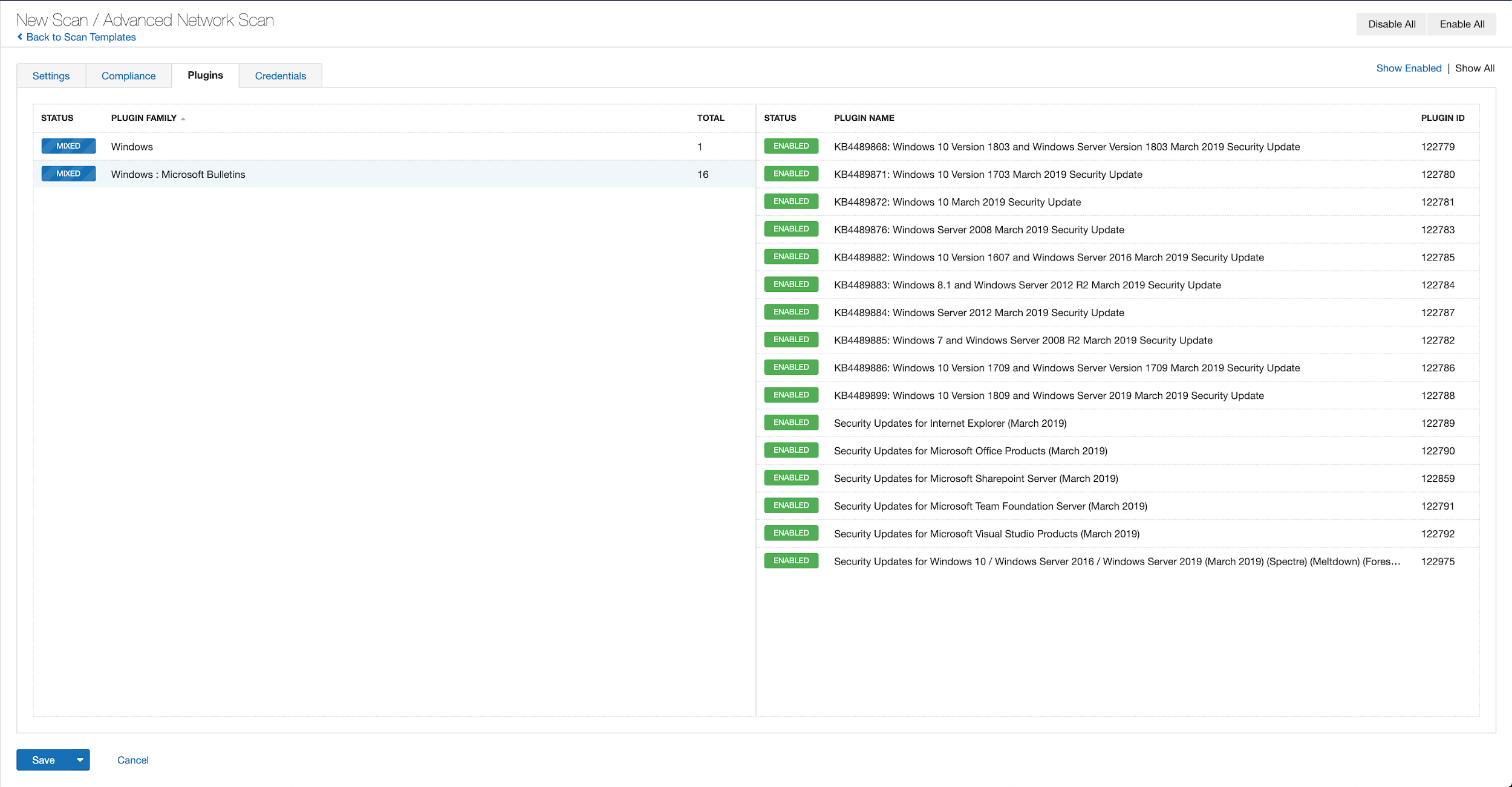
With that filter set, click on the plugin families to the left, and enable each plugin that appears on the right side. Note that if your families on the left say Enabled then that means all of the plugins in that family are set. Disable the whole family before selecting the individual plugins for this scan. Here’s an example from Tenable.io:
A list of all of the plugins released for Tenable’s November 2019 Patch Tuesday update can be found here. As always, we recommend patching systems as soon as possible and regularly scanning your environment to identify those systems that are yet to be patched.
As a reminder, Windows 7 support will be discontinued on January 14, 2020, so we strongly recommend reviewing what hosts remain and any action plans for migration. Plugin ID 11936 (OS Identification) can be useful for identifying hosts that are still running on Windows 7.
取得更多資訊
- Microsoft’s November 2019 Security Updates
- Tenable plugins for Microsoft November 2019 Patch Tuesday Security Updates
- CERT Vulnerability Note VU#125336 for CVE-2019-1457
加入 Tenable Community 的 Tenable 安全回應團隊。
深入瞭解 Tenable,這是用於全面管理新型攻擊破綻的首創 Cyber Exposure 平台。
Get a free 60-day trial of Tenable.io Vulnerability Management.
深入瞭解
- Vulnerability Management




Tenable One
申請示範
以 AI 技術為後盾的全球領先曝險管理平台。
感謝您
感謝您對 Tenable One 有興趣。
我們的人員將盡快與您聯絡。
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success