Tenable
Security Center
利用全球首屈一指的內部管理弱點管理解決方案辨識並解決您的網路弱點。
降低 IT/OT 基礎架構的風險。開創該領域的解決方案持續提升標準,以保護企業免於會增加企業風險的重大網路曝險。
全球首屈一指的內部管理弱點管理解決方案
Tenable Security Center 套裝軟體
Tenable Security Center 套裝軟體產品可量身訂做以滿足您的需求,提供您了解風險和優先修復弱點所需的能見度與背景資訊。
Tenable Security Center
- 內部部署的風險型弱點管理
- Nessus 掃描器數量無限制,即刻提供網路能見度
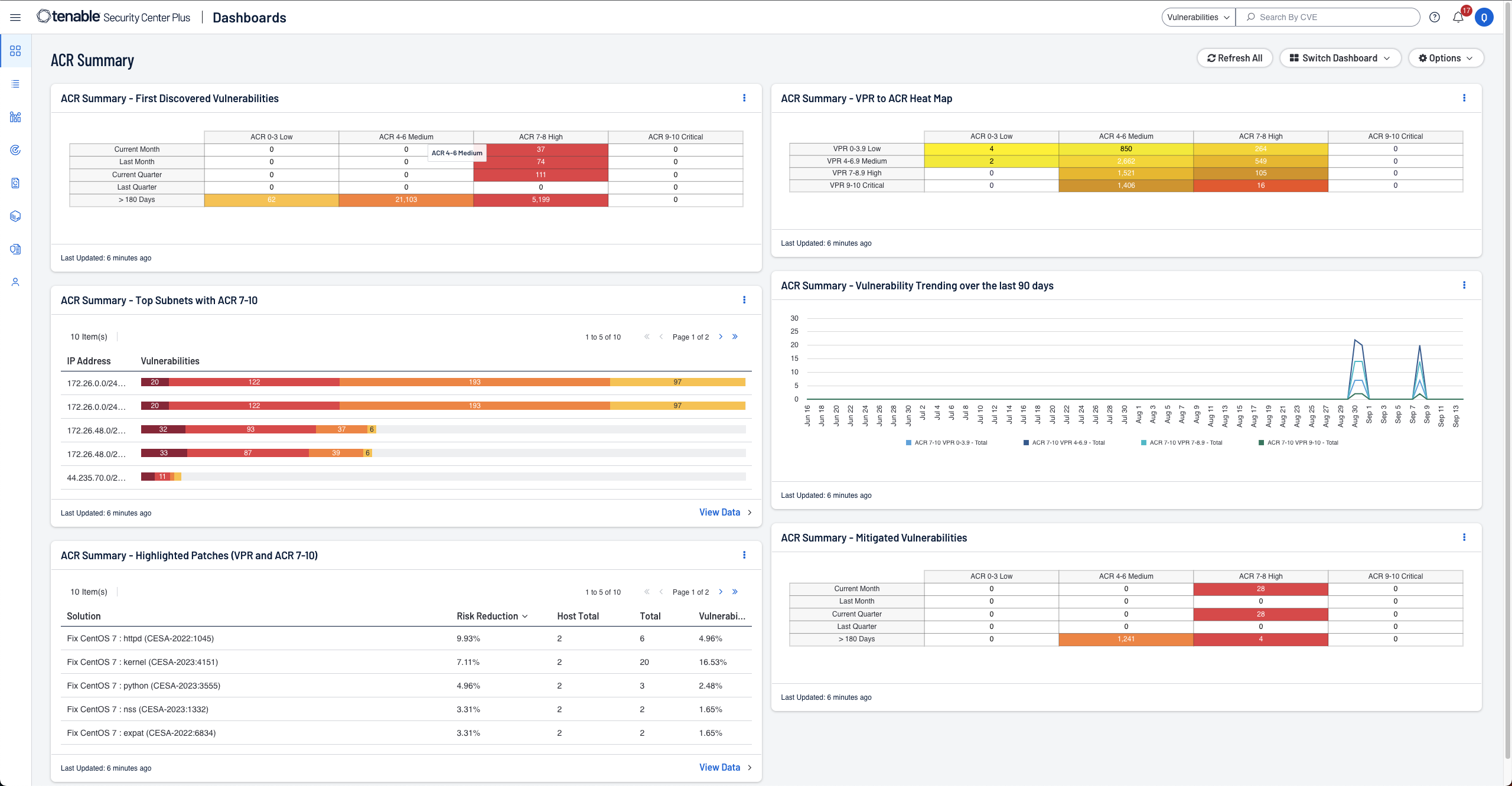
- 運用高度可自訂的儀表板、報告和工作流程,取得更清楚、更可行的資料深入分析結果
- 利用內建的風險評分與情境式威脅情報,立即辨識弱點及排定優先順序
- 具備可自訂的設定警示、通知和工單功能,能加速資安事端的回應
- 可免費存取 API 進行客戶整合、資料擷取,並使資料更加完善
- 搜尋您外部攻擊破綻中的未知資產
Tenable Security Center Director
針對擁有多個 Tenable Security Center 主控台的客戶來說,Tenable Security Center Director 可作為 Tenable Security Center 或 Tenable Security Center Plus 的附加元件。
- 涵蓋所有 Tenable Security Center 主控台檢視與管理網路的單一管理平台
- 從單一集中位置輕鬆檢視每一個 Tenable Security Center 主控台的掃描工作
- 集中化的深入解析,可協助製作報告及維持多個主控台、掃描器與資產的持續運作
- 涵蓋多個 Tenable Security Center 主控台的集中化報告,讓您易於衡量您的網路風險
快速衡量及分析安全性與合規性風險
Tenable Security Center 評論
Tenable 是唯一一家在 2025 年 Gartner® Peer Insights™ 弱點評估客戶之聲中獲得客戶最佳選擇獎的廠商。

tenable one
全球唯一以 AI 技術為後盾的曝險管理平台
Tenable One 透過統一整個攻擊破綻上的安全能見度、深入解析和行動來降低網路風險,協助企業快速發現並修復重大弱點。
Tenable Security Center 已成為我們網路的真理之聲,它提供額外的深入解析,讓我們能夠負起責任,並向我們的董事會證明我們的安全方案成效卓著。
常見問題
-
什麼是 Tenable Security Center?
-
Tenable Security Center 和 Tenable Security Center Plus 是 Tenable 的內部部署弱點管理解決方案。Tenable Security Center 系列產品建構在領先業界的 Nessus 技術之上,可發現、調查及安排弱點的優先順序,讓您掌握其安全和合規性態勢的風險局面。如需有關這些解決方案的更多資訊,請參閱 Tenable Security Center 產品說明和 Tenable Security Center Plus 產品說明。
-
Tenable Security Center 和 Tenable Security Center Plus 之間有何差異?
-
Tenable Security Center Plus 是一套以 Tenable Security Center 的功能為基礎而打造的弱點管理平台,並包含了更多的風險指標,例如:Asset Criticality Rating (ACR),能夠為您的資產與弱點提供多一層的背景資訊。這些指標為您的弱點管理方案提供了更量身訂做的方式,而且全都在 Tenable Security Center Plus 執行個體上計算,因此您的資料仍會保留在內部。此外,Tenable Security Center Plus 能夠與 Tenable 的曝險管理平台 Tenable One 整合,提高 Security Center Plus 所提供的深入解析的價值。
-
Tenable Security Center 能夠與 Tenable One 搭配運作嗎?
-
有的!Tenable Security Center Plus 與 Tenable One 整合,可提供混合的弱點管理部署,並可讓內部部署客戶充分利用曝險管理平台所帶來的優勢。
-
Tenable One 是什麼?
-
Tenable One 是一款曝險管理平台,可協助企業掌握現代攻擊破綻的能見度、致力於防範可能的攻擊,同時準確地傳達網路風險,使企業發揮最佳績效。這個平台結合了跨 IT 資產、雲端資源、容器、Web 應用程式和身分系統等最廣泛的弱點涵蓋範圍,建構在 Tenable Research 弱點涵蓋範圍速度與廣度的基礎上,並新增了可排定處置措施優先順序並傳達網路風險的全方位分析功能。 使用 Tenable One 可為企業創造以下優勢:
- 取得整個現代攻擊破綻的全方位能見度
- 預測安全威脅並為防範攻擊的措施排定優先順序
- 傳達網路風險,藉此制定更明智的決策。
-
什麼是 Tenable Security Center Director?
-
Tenable Security Center Director 是 Tenable Security Center 的一項附加元件。它能橫跨多個 Tenable Security Center 主控台提供大型企業客戶其大型且通常分散的網路環境的統一檢視畫面。Tenable Security Center Director 可提供執行個體的完整能見度與管理功能,讓您專注在弱點管理上,並減少系統管理工作上的負擔。
-
Tenable Security Center 能夠與 Tenable Web App Scanning 搭配運作嗎?
-
利用 Tenable Security Center,Tenable 透過增添內部部署 Web 應用程式安全性來強化您的防禦能力。由於 Tenable Web App Scanning 嚴密整合至 Security Center 使用者介面,能讓您判別和解決您所有網路與 Web 應用程式的弱點,加強您的安全態勢並且在現場管理您的資料。
Tenable Web App Scanning 是一套動態應用程式安全測試 (DAST) 工具,能徹底評估 Web 應用程式。它能夠梳理 Web 應用程式以建立網站地圖,然後掃描前端來偵測自訂程式碼及第三方元件中的弱點。
-
什麼是 Predictive Prioritization?它如何協助排定弱點的處理優先順序?
-
Predictive Prioritization 將 Tenable 收集得來的弱點資料與第三方弱點及威脅資料結合,並利用 Tenable Research 開發的先進資料科學演算法一併加以分析。每一個弱點都會得到一個弱點優先順序評分 (簡稱 VPR),代表攻擊者在未來 28 天內可能會對特定弱點進行刺探利用的可能性以及其嚴重性。您可以利用 VPR 來瞭解弱點在獨特環境中的實際網路風險,因此您就可以優先修復會造成最嚴重影響的弱點。
-
Tenable Security Center 如何搜尋資產與弱點?
-
Tenable Security Center 採用各種不同的感應器,確保即時持續搜尋與評估您的網路、資產和弱點。
Tenable Security Center 會使用以下來源收集貴公司所有的安全資料,例如:
- 被動監控: 即時監控網路流量和活動可得知資產是否與網路連線以及它們之間的通訊方式等相關資訊。它能分辨新的或從未出現過的裝置或應用程式,並在可疑行為出現的當下偵測出來。
- 主動掃描: 徹底分析資產狀態以確定其弱點、錯誤設定、惡意軟體和其他弱點。
- 主機資料: 主動監控主機活動和事件,包括存取及變更的深入解析。
- 智慧型介接軟體:Tenable Security Center 能充分運用您的其他安全投資,整合其他的安全資料,以改善背景資訊與分析。這兩者都會分析來自各種資料來源的資訊,包括:Active Directory (AD)、設定管理資料庫 (CMDB)、修補程式管理系統、行動裝置管理 (MDM) 系統、雲端平台、Web 應用程式等等。
- 代理程式掃描: 立即稽查暫時性或難以掃描的資產,這些資產會在無憑證的情況下間歇性地與網路連線。安裝完畢後,代理程式無需一直使用主機憑證即可執行經認證的掃描。
-
What are Tenable Agents? 它們與 Tenable Security Center 如何搭配運作?
-
Tenable Agents are lightweight programs installed locally on a host — a laptop, virtual system, desktop and/or server. 代理程式從 Nessus Manager 中央伺服器接收掃描指令,在本機進行掃描,再將弱點、合規性和系統結果回報給中央伺服器。 Tenable Agents are available with Tenable Vulnerability Management and Tenable Security Center.
Tenable Agents with Tenable Security Center increase scan coverage and remove blind spots by making it easier to scan problematic assets such as those needing ongoing host credentials and offline assets. 代理程式還能啟動大規模並行掃描,且對網路產生很小的影響。
For more information on Tenable Agents, see the following resources:
-
Tenable Security Center 能夠偵測多少不同類型的弱點?
-
Tenable Research 是 Tenable Security Center 的技術後盾,提供世界級的網路威脅情報、資料科學深入解析、警示和安全公告。Tenable 擁有業界最豐富的弱點和情報資料組,以及最多的 CVE 涵蓋範圍,自 2019 年 1 月起已涵蓋超過 79,000 個 CVE 並發現超過 476 個零時差弱點。 Tenable 每天都會在新的弱點出現時更新其弱點資料庫。Tenable Research 每週執行 100 多次新偵測。
-
Tenable Security Center 偵測到弱點後會如何處理?
-
當 Tenable Security Center 偵測到弱點後,它會提供您每一個偵測到的弱點的詳細深入解析,包括:
- 弱點資訊: Name and description of the vulnerability, remediation guidance, date of discovery and date of last vulnerability observation, CPE, date patch published, patching status, plugin ID and details.
- 主機資訊: Host name, affected hosts, IP address, DNS, Mac address, NetBIOS, repositor.
- 風險資訊: Vulnerability severity, VPR score, CVSS score and vectors, vulnerability age, known exploits, exploit code maturity, product coverage, threat intensity, threat recency, threat sources, percentage risk reduction associated with patching.
-
Tenable Security Center 有哪些報告功能?
-
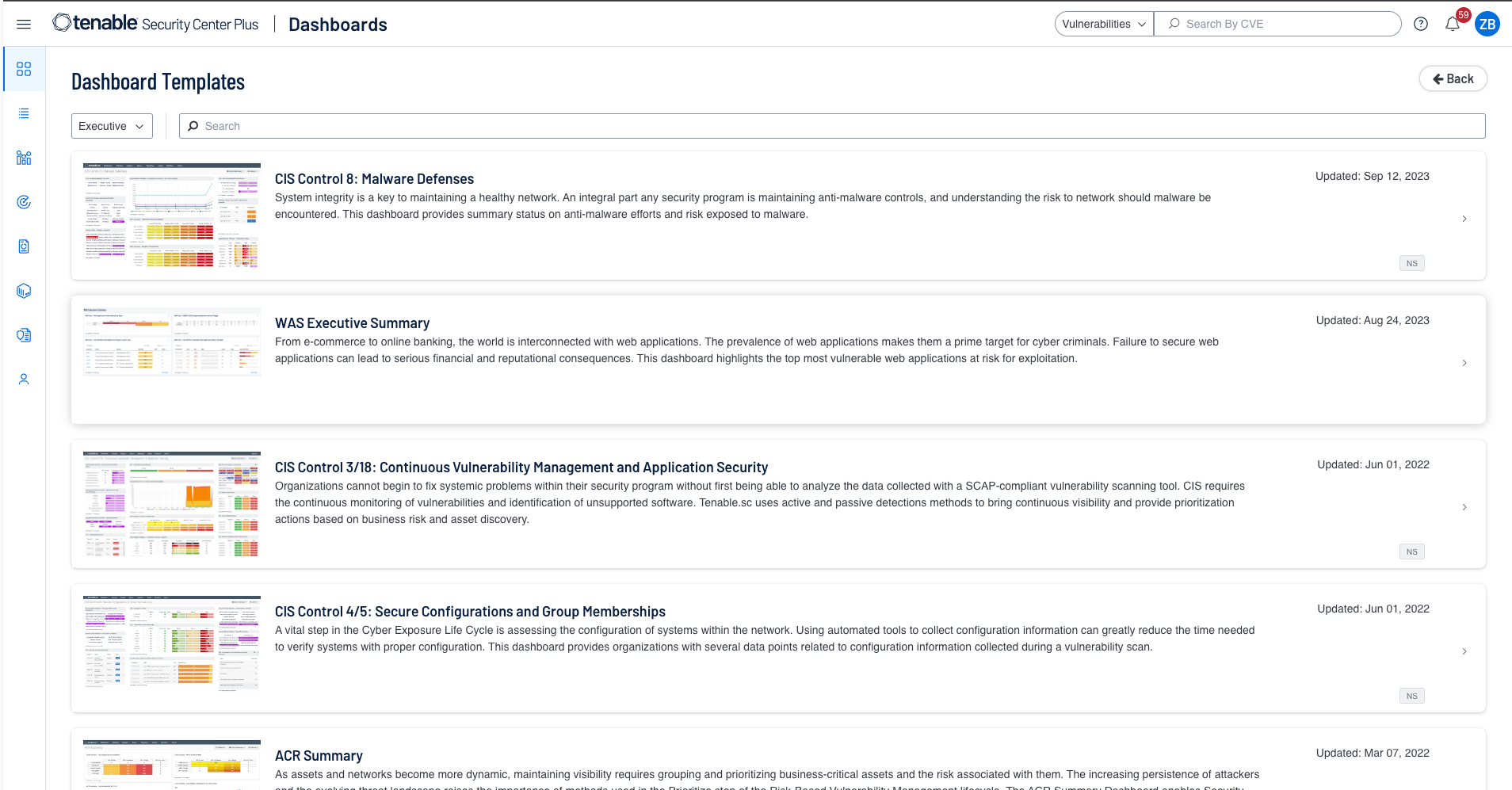
Tenable Security Center 提供非常彈性的報告功能,運用超過 350 個預先盡力的範本和方便使用的報告建立介面,可輕鬆建立自訂報告。以 HTML5 為基礎的報告可合併來自您整個企業的資料,因此您就可以衡量與分析您的安全方案成效。利用現有的範本可完全自訂資料,方法是刪除或新增某些元件或調整篩選條件,藉此製作符合企業各種需求的報告。
可製作多份報告,自訂每一份報告的內容,以各種角度分析所收集的資料,製作出對企業內的相關團隊或決策者更具參考價值且更即時的報告。報告的呈現方式可能從鉅細靡遺到深入摘要等,不一而足。報告可採用標準的 PDF 和 CSV 格式。您可以排程及自動以電子郵件寄出報告、分享給一個以上的指定主控台使用者和/或在完成時公布在一個以上的網站。
您也可以使用 Tenable Security Center 完備且自動地報告您的網路是否符合複雜的合規標準,例如:PCI 和 NIST。
-
Tenable Security Center 可協助維持合規性嗎?
-
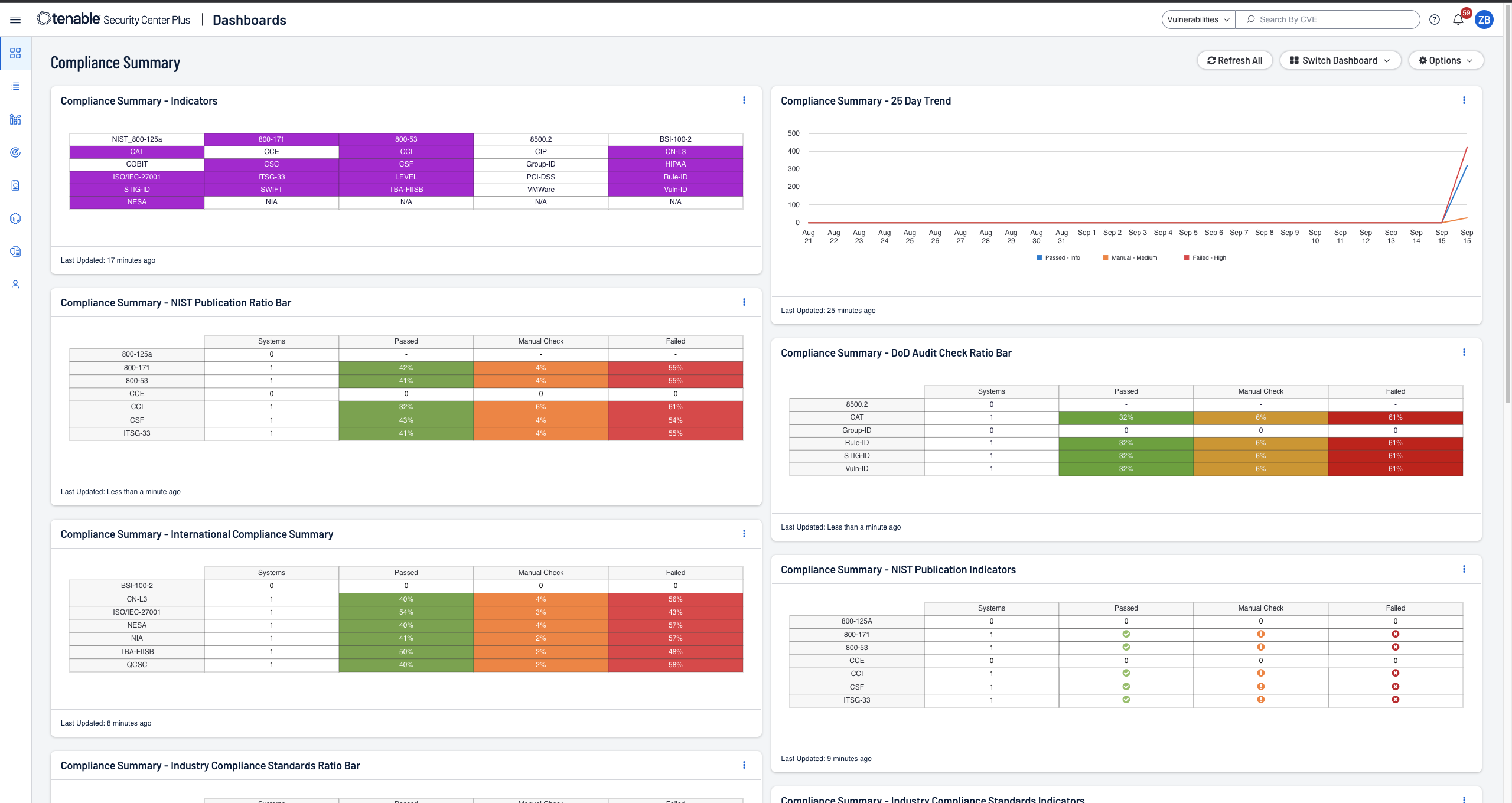
沒錯,Tenable Security Center 可協助維持合規性。它能立即提供您合規性狀態的能見度,讓您隨時保持合規。您可以使用預先定義的檢查輕鬆展現您是否遵循產業標準與法規要求,例如:ISO/IEC 27001/27002、PCI、NIST Cybersecurity Framework、NIST SP 800-171 和 CIS Critical Controls。
Tenable Security Center 針對領先市場的安全標準與合規要求提供立即可用、可完全自訂的報告和儀表板。您可以「依現況」使用報告或輕鬆量身訂做,以符合您特定的安全與業務需求。例如,您可以為各事業部輕鬆建立特定的報告和儀表板。
-
什麼是 Tenable AI Aware?
-
Tenable AI Aware 是 Tenable Vulnerability Management 和 Tenable Security Center 當中的一項功能,可協助企業監控與減緩與快速採用 AI 技術所產生的相關風險。它運用進階的偵測技術,包括代理程式、被動式網路監控、動態應用程式安全測試和分散式掃描引擎,能夠發掘您企業中未經授權的 AI 解決方案、偵測 AI 弱點,並且讓非預期的 AI 或大型語言模型 (LLM) 開發無所遁形。AI Aware 提供了一種全方位的安全優先方式,透過提供深入整個企業數位生態體系中的 AI 軟體、程式庫與瀏覽器外掛程式的能見度來管理 AI 相關風險。由此深入瞭解 Tenable AI Aware。
-
何謂外部攻擊破綻管理 (External Attack Surface Management,簡稱 EASM)?
-
External Attack Surface Management s a capability offered by Tenable that provides visibility into blind spots outside of your network perimeter. 它能讓客戶掃描其網域,找出之前未知的網際網路連線資產,這些資產可能會為貴公司帶來高風險。
-
外部攻擊破綻管理包含在 Tenable Security Center 當中嗎?
-
是的,Tenable Security Center 提供外部攻擊破綻管理功能。如果您需要在結果中包含更多網域、頻率和/或中繼資料,您必須購買我們的 Tenable Attack Surface Management 附加元件。
-
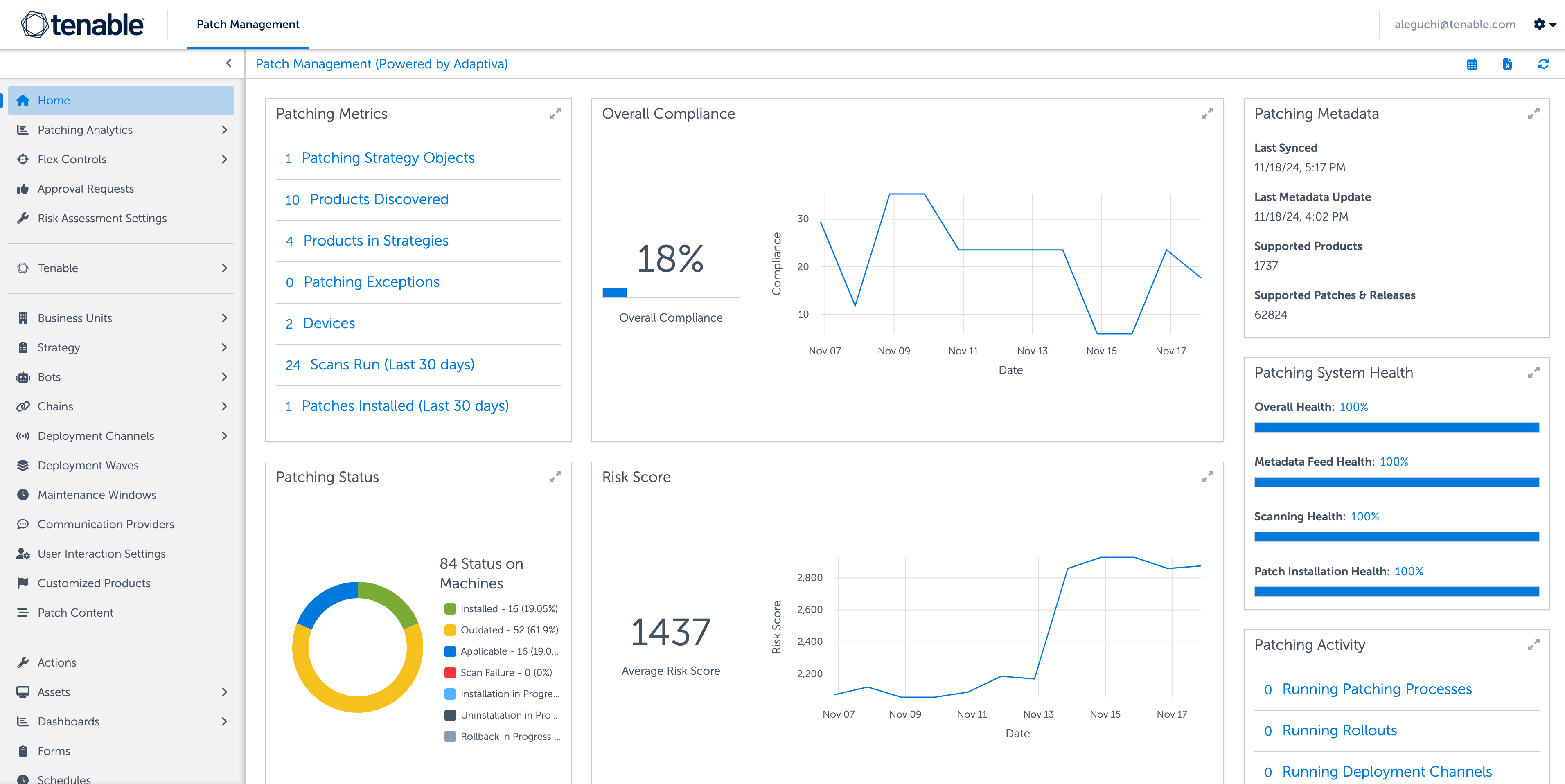
什麼是 Tenable Patch Management?
-
Tenable Patch Management 是一款修補程式管理模組,將 Tenable 領先市場的優先排序功能與自主管理的修補功能互相搭配。弱點與最新修復動作之間的自動化關聯分析,能協助您的團隊克服可能會發生在弱點優先排序與修復工作之間的瓶頸。Tenable Patch Management 為擴充與縮減規模以滿足任何企業的需求而打造,它能讓您的企業利用部署、測試、核准、和應用程式等的精細度精準管理設定。
若想利用 Tenable Patch Management,您需要 Tenable Vulnerability Management、Tenable Security Center、Tenable One 或 Tenable Enclave Security 的授權。在此深入瞭解。
-
Tenable Security Center 有與其他產品整合嗎?
-
沒錯,Tenable Security Center 有與其他產品整合。該套裝軟體提供立即可用的整合性,可充分運用 Tenable 的弱點洞察力來整合工單、修補程式管理、SIEM、SOAR 及其他第三方產品。造訪技術生態體系頁面可深入瞭解各種可用的整合功能與生態體系合作夥伴。您也可以使用 Tenable Security Center 的 API 開發自訂整合功能。
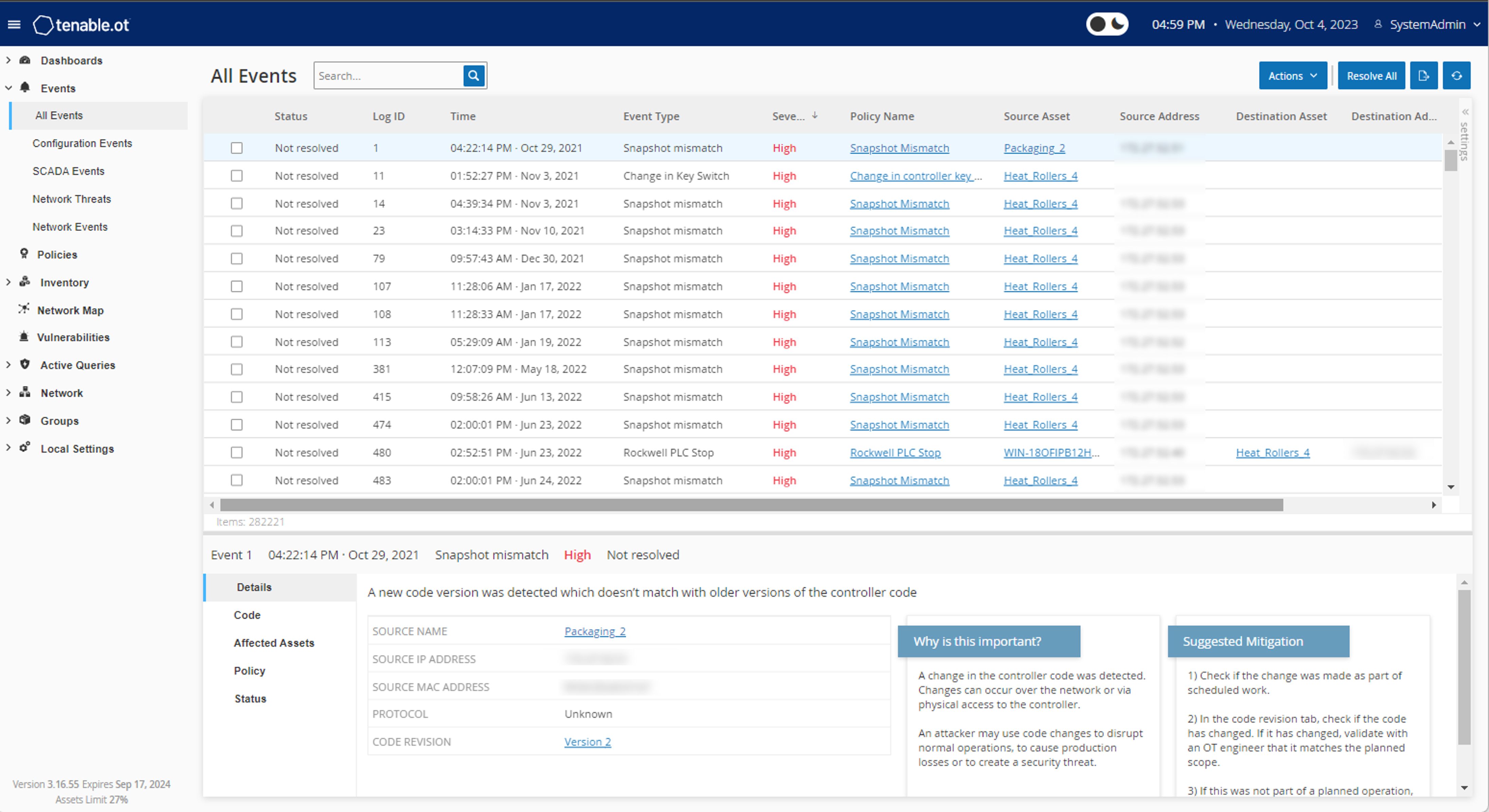
此外,Tenable Security Center 還擁有與 Tenable OT Security、Tenable Web App Scanning 和 Tenable Patch Management 的內建整合功能。 Tenable Security Center Plus 能夠與 Tenable One 整合,提供混合多元弱點管理部署,並且讓內部部署客戶享受鋪險管理平台帶來的優勢。
-
Tenable Security Center 如何定價與授權?
- Tenable Security Center 是以年度訂閱方式授權,並且依 IP 數量定價。亦可購買永久授權。
-
我可以在何處找到 Tenable Security Center 說明文件?
-
您可以在 https://docs.tenable.com/ 找到 Tenable Security Center 及所有 Tenable 產品的技術說明文件。
-
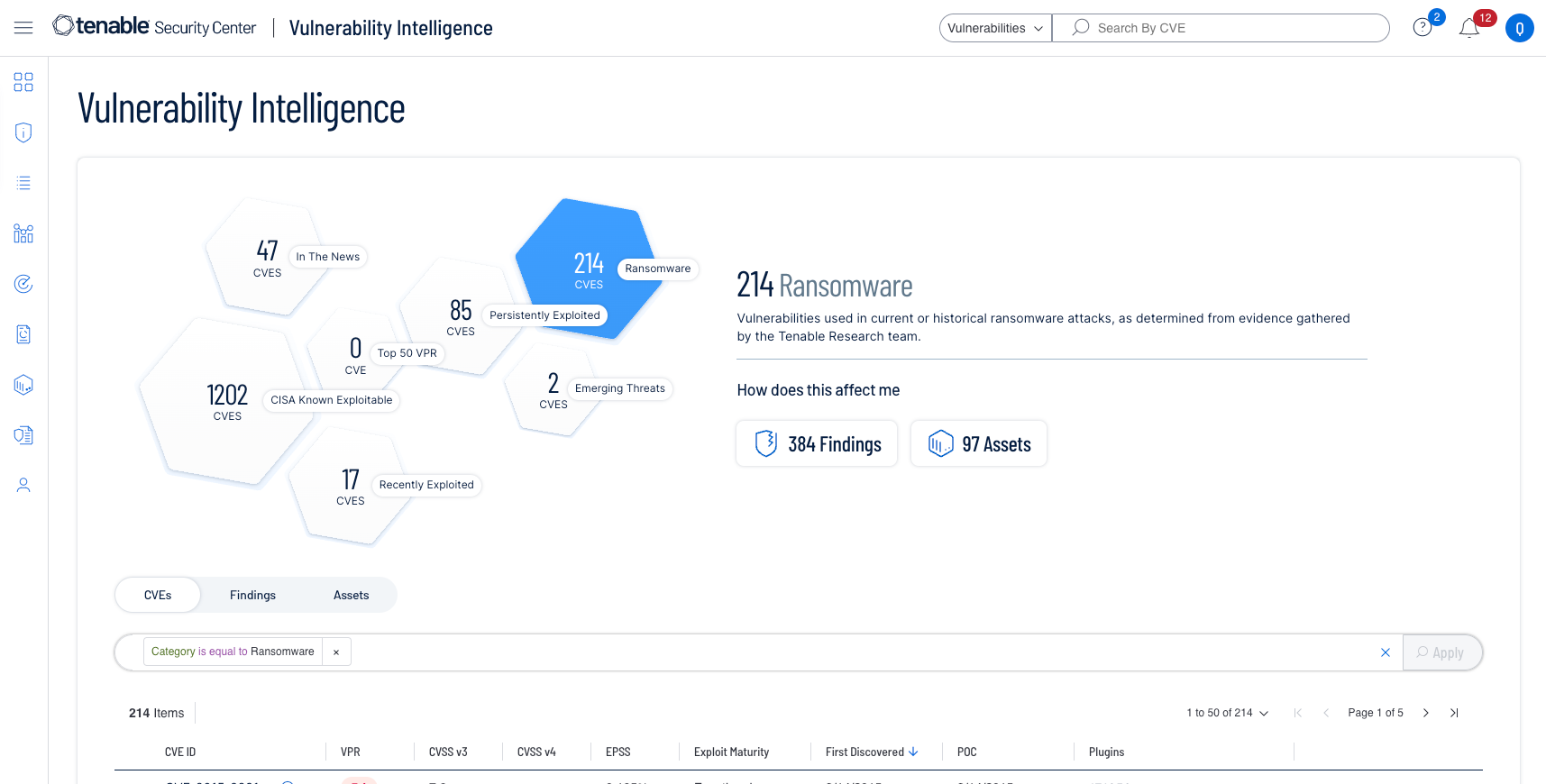
什麼是 Vulnerability Intelligence (弱點情資)?
-
Vulnerability Intelligence 結合外部資料來源和內部弱點資料,提供可採取行動的弱點管理深入解析。Vulnerability Intelligence 提供任何特定弱點的重要背景資訊,以了解遭攻擊者利用的可能性及其對您環境的影響。
Vulnerability Intelligence (弱點情資) 能將 Tenable 豐富的弱點研究資訊、資料科學深入解析、安全應變和您的弱點管理資料整合在一個統一的位置。您可以輕鬆地根據這些豐富的情報來搜尋、獲得背景資訊以及應變弱點,並向管理層報告弱點對貴公司的影響。







Tenable One
申請示範
以 AI 技術為後盾的全球領先曝險管理平台。
感謝您
感謝您對 Tenable One 有興趣。
我們的人員將盡快與您聯絡。
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success