ThemeGrill Demo Importer Vulnerability Actively Exploited in the Wild
Severe vulnerability in ThemeGrill Demo Importer WordPress plugin is being actively exploited in the wild. Users should upgrade to version 1.6.3 ASAP.
背景說明
The ThemeGrill Demo Importer WordPress plugin allows users to import ThemeGrill theme demos in one click. Versions 1.3.4 to 1.6.2 are vulnerable to a remote unauthenticated database wipe and authorization bypass vulnerability. Users are encouraged to upgrade to version 1.6.3 as active attacks have been reported in the wild against users on 1.6.2 and below.
分析
On February 15, WebARX disclosed a vulnerability in the ThemeGrill Demo Importer for WordPress, which could allow an unauthenticated, remote attacker to execute administrator functions, including reverting all the site’s settings back to their default configuration and wiping all the database tables.
To exploit this vulnerability, a ThemeGrill theme must be installed and activated on a site. If there is an administrative user with the username ‘admin,’ then an attacker will also be automatically logged in as ‘admin’ after the site is wiped.
概念驗證
There is no public proof of concept (PoC) available at this time, but attacks have been reported by WebARX, and a list of known malicious IPs can be found at the bottom of the WebARX disclosure page.
Vendor response
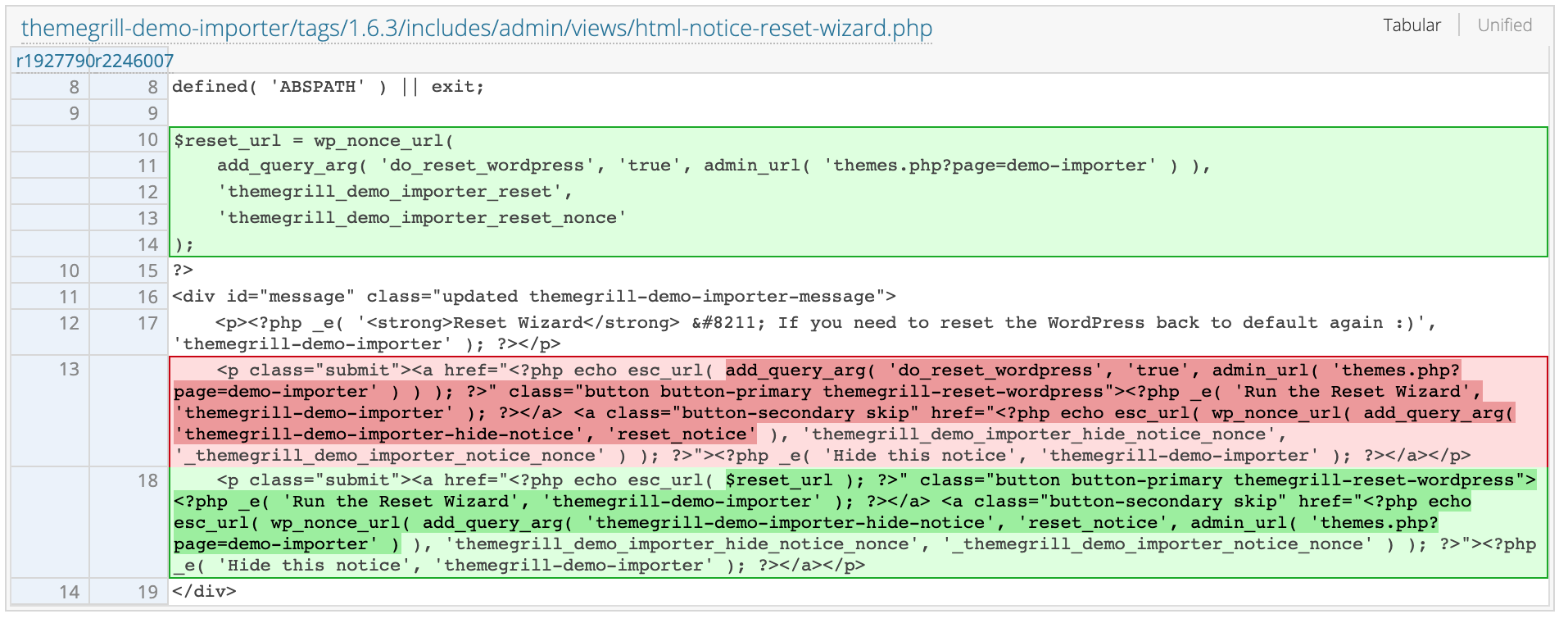
On February 16, ThemeGrill released 1.6.2 to address this vulnerability. However, ThemeGrill released version 1.6.3 on February 18 to address issues with the initial fix. Version 1.6.3 removes the automatic invocation of a full reset, and instead directs the user to the plugin’s reset wizard. This comes after reports that users on version 1.6.2 were still being exploited.
解決方法
At the time of publication, there is no known effective workaround that would not disrupt functionality of the plugin. Users are encouraged to upgrade to version 1.6.3 of the plugin for mitigation.
找出受影響的系統
A list of Tenable plugins to identify this vulnerability will appear here as they’re released.
取得更多資訊
- ThemeGrill Demo Importer WordPress Plugin Page
- WebARX Disclosure Page
- ThemeGrill Demo Importer 1.6.3 Source Changes
加入 Tenable Community 的 Tenable 安全回應團隊。
深入瞭解 Tenable,這是用於全面管理新型攻擊破綻的首創 Cyber Exposure 平台。
索取 Tenable.io Vulnerability Management 的 30 天免費試用。
- Vulnerability Management

