CVE-2020-1472:Netlogon Could 中的「Zerologon」弱點能讓攻擊者綁架 Windows 網域控制站
Security researchers reveal how the cryptographic authentication scheme in Netlogon can be exploited to take control of a Windows domain controller (DC).
Update: September 21, 2020: The ‘Identifying Affected Systems’ section has been updated to include instructions for our new unauthenticated check for Zerologon.
Update: October 02, 2020: The ‘Identifying Affected Systems’ section has been updated to highlight the release of the Zerologon scan template for Nessus and Tenable.io.
背景說明
On September 11, researchers at Secura published a blog post for a critical vulnerability they’ve dubbed “Zerologon.” The blog post contains a whitepaper explaining the full impact and execution of the vulnerability, identified as CVE-2020-1472, which received a CVSSv3 score of 10.0, the maximum score. Zerologon was patched by Microsoft in the August Patch Tuesday round of updates. This disclosure follows a previous Netlogon related vulnerability, CVE-2019-1424, which Secura detailed at the end of last year.
分析
CVE-2020-1472 is a privilege escalation vulnerability due to the insecure usage of AES-CFB8 encryption for Netlogon sessions. The AES-CFB8 standard requires that each byte of plaintext, like a password, must have a randomized initialization vector (IV) so that passwords can’t be guessed. The ComputeNetlogonCredential function in Netlogon sets the IV to a fixed 16 bits, which means an attacker could control the deciphered text. An attacker can exploit this flaw to impersonate the identity of any machine on a network when attempting to authenticate to the Domain Controller (DC). Further attacks are then possible, including the complete takeover of a Windows domain. Secura’s whitepaper also notes that an attacker would be able to simply run Impacket’s ‘secretsdump’ script to pull a list of user hashes from a target DC.
In order to exploit this vulnerability, the attacker would need to launch the attack from a machine on the same Local Area Network (LAN) as their target. A vulnerable client or DC exposed to the internet is not exploitable by itself. The attack requires that the spoofed login works like a normal domain login attempt. Active Directory (AD) would need to recognize the connecting client as being within its logical topology, which external addresses wouldn’t have.
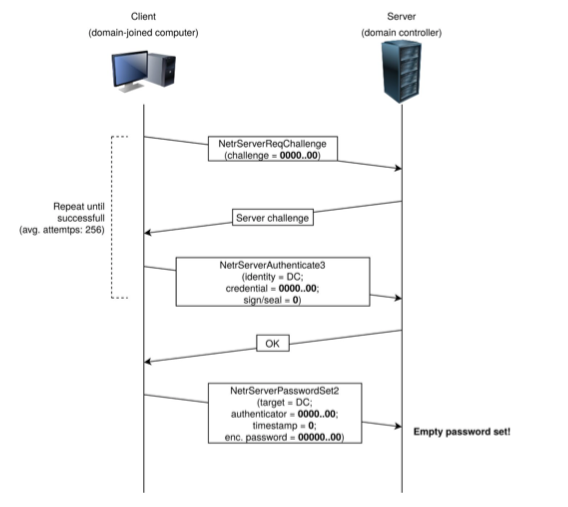
Image source: Secura CVE-2020-1472 Whitepaper
概念驗證
Several proofs of concept (PoCs) have been published to GitHub [1] [2] [3] [4] which demonstrates wide interest and experimentation across the security community. Researchers have been fast at work to confirm successful exploitation. Critical and high profile vulnerabilities tend to receive widespread interest from security researchers and attackers alike.
In a hypothetical attack, one could use this vulnerability to deploy ransomware throughout an organization and maintain a persistent presence if cleanup and restoration efforts miss any additional malicious scripts. Organizations with network-accessible backups could end up with a perfect storm if a ransomware group destroys backups to increase their likelihood of payout from the victim organization.
解決方法
Applying the August Patch Tuesday update from Microsoft's Advisory will fix the vulnerability by enforcing remote procedure call (RPC) in the Netlogon protocol for all Windows devices. Tenable strongly encourages users and admins alike to apply this patch as soon as possible.
Yeah, I can confirm that this public exploit for Zerologon (CVE-2020-1472) works. Anybody who has not installed the patch from August's Patch Tuesday already is going to be in much worse shape than they already were.https://t.co/SWK2hUDOYc https://t.co/0SDFfageQC pic.twitter.com/Lg8auMdtVU
— Will Dormann (@wdormann) September 14, 2020
Users should be aware that Microsoft notes a revision to this advisory will be coming on February 9, 2021, and that, once the enforcement phase begins, enforcement mode will be required for all non-Windows devices. Administrators can manually allow specific devices through group policy for legacy device needs.
找出受影響的系統
A list of Tenable plugins to identify this vulnerability can be found here. Tenable will also be releasing additional plugins for the February 9, 2021, update. A compliance audit file, available here, can be used to ensure that the FullSecureChannelProtection registry key value is set in group policy on the DC. The August 2020 fix should set this registry key after the patch has successfully been applied.
Tenable has also released Microsoft Netlogon Elevation of Privilege, an unauthenticated plugin for customers that would like to scan their DCs to test exploitability. This plugin attempts to authenticate to the target using an all zero client credential after providing an all zero client challenge. On vulnerable targets, this will succeed on average once every 256 attempts, and this plugin will attempt this up to 2000 times in order to verify if the target is affected. Due to the number of login attempts required to accurately verify exploitability of a target, Tenable does not recommend running this plugin alongside any other plugins in a scan, as it is intended for single-target Domain Controller scans. To enable the plugin, users must disable the 'Only use credentials provided by the user' setting under the Brute Force section in the Assessment options in their scan configuration.
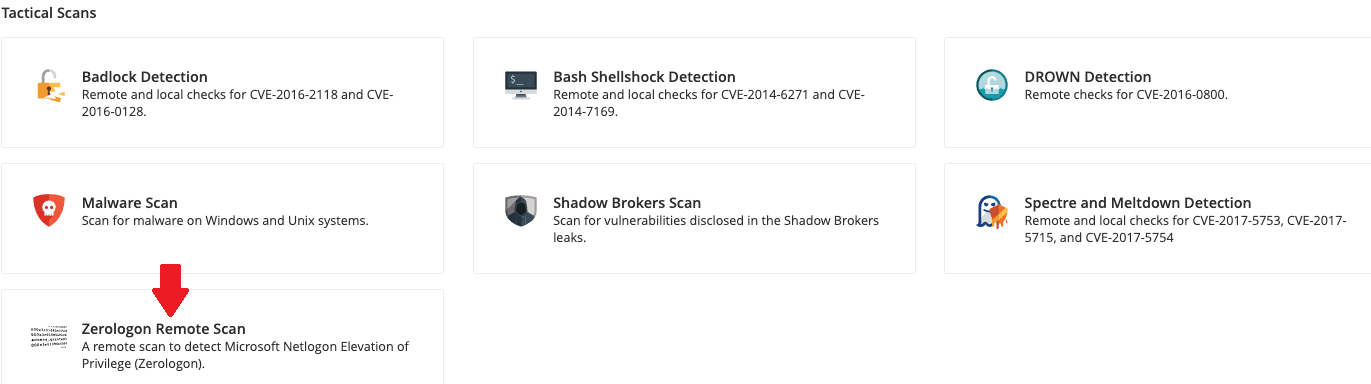
Tenable.io and Nessus users will also be able to take advantage of the new scan template dedicated to targeting Zerologon. Plugin 140657 and its dependencies are automatically enabled within the template, and it also comes with the necessary brute force settings automatically configured.
取得更多資訊
- Tenable's August 2020 Patch Tuesday Blog
- Secura's Zerologon Whitepaper
- Microsoft Guidance on "How to manage the changes in Netlogon secure channel connections associated with CVE-2020-1472
加入 Tenable Community 的 Tenable 安全回應團隊。
深入瞭解 Tenable,這是用於全面管理新型攻擊破綻的首創 Cyber Exposure 平台。
Get a free 30-day trial of Tenable.io Vulnerability Management.
- Vulnerability Management
- Vulnerability Scanning


