by Steve Tilson
May 11, 2017
As the utilization of Virtual Private Network (VPN) technology grows with organizations leveraging remote workers, so does the security risk of unauthorized or malicious access to the network. Tracking insiders through log analysis and account auditing is a key component that assists in identifying intrusions. Elements in this report provide information for monitoring and tracking VPN activity by leveraging data correlated by Tenable Log Correlation Engine® (LCE®), Tenable SecurityCenter® is able to provide detailed insight into the VPN activity present in the organization.
A virtual private network (VPN) extends a private network across a public network, and enables users to send and receive data across shared or public networks A VPN creates a secure encrypted connection and tunnels traffic in which applications running may benefit from the functionality, security and management of the private network. The encrypted connection protects the data in transit, thus preventing attackers from accessing files and other sensitive information. However, strong passwords, authentication measures and secure protocols are not always enough to protect against threats. The need to understand where users are connecting from is critical to maintaining a secure network.
This report gives analysts a visual representation of VPN usage over time, including user summaries and logins from unusual sources. The VPN_Login_From_Unusual_Sources normalized event monitors several VPN login events and is triggered when a user connects from a new source IP address. Triggered events could be the result of compromised VPN accounts, or users that have moved locations. Although VPN connections are encrypted, once an attacker has established a connection to the environment, the use of encryption does not provide security. Therefore, all VPN connections should be monitored carefully for unusual activity. This report provides details that track users through log analysis and account auditing. The information found provides details about VPN events and account activity.
This report is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards and assets. The report can be easily located in the SecurityCenter Feed under the category Monitoring. The report requirements are:
- SecurityCenter 5.4.5
- LCE 5.0.1
Tenable constantly analyzes information from our unique sensors, delivering continuous visibility and critical context and enabling decisive action that transforms the security program from reactive to proactive. By using the Log Correlation Engine (LCE), the organization can perform deep log analysis detecting possible systems with elevated risk. With more supported technologies than other vendors, SecurityCenter Continuous View® (SecurityCenter CV™) is able to analyze vulnerabilities and collected logs from a wide range of operating systems, network devices, hypervisors, databases, elements, phones, web servers and critical infrastructure devices. Tenable enables powerful, yet non-disruptive, continuous monitoring that will provide organizations with the information needed to detect and remediate vulnerabilities within the enterprise.
This report contains the following chapters:
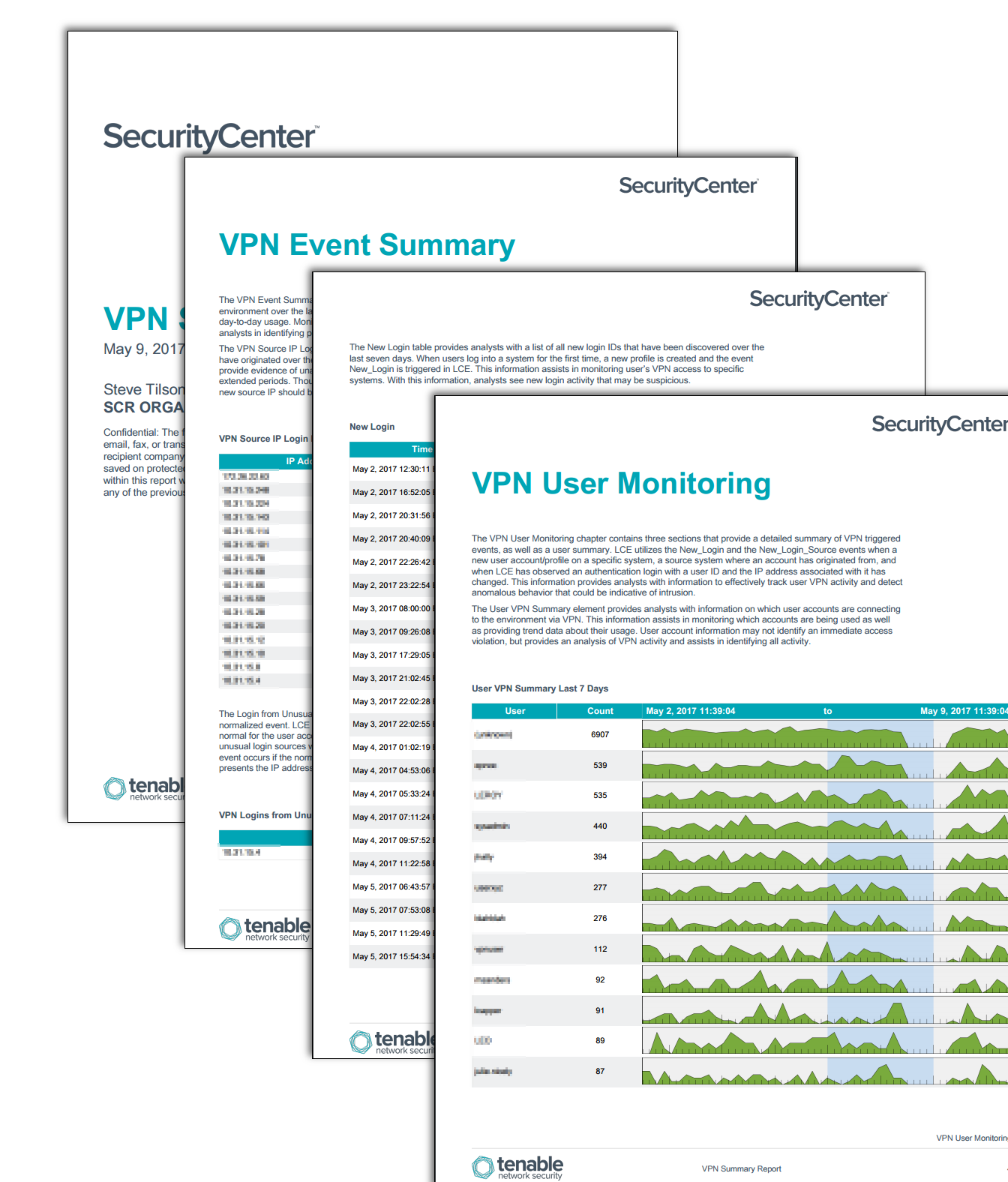
Executive Summary: The Executive Summary provides leadership with an overall VPN analysis. Information found in this report provides insight into the utilization of all VPN activity while monitoring this activity in the environment. Elements in this report break down event log information to provide further details.
VPN User Monitoring: The VPN User Monitoring chapter contains three sections that provide a detailed summary of VPN triggered events, as well as a user summary. LCE utilizes the New_Login and the New_Login_Source events when a new user account/profile on a specific system, a source system where an account has originated from, and when LCE has observed an authentication login with a user ID and the IP address associated with it has changed. This information provides analysts with information to effectively track user VPN activity and detect anomalous behavior that could be indicative of intrusion.
VPN Event Summary: The VPN Event Summary chapter presents the analyst with detailed information about VPN events in the environment over the last seven days. These detailed event logs provide analysts with information on user’s day-to-day usage. Monitoring known and unknown IP sources, along with normalized VPN events, assists analysts in identifying possible intrusions or breaches, as well as utilization.