by Michael Willison
September 12, 2014
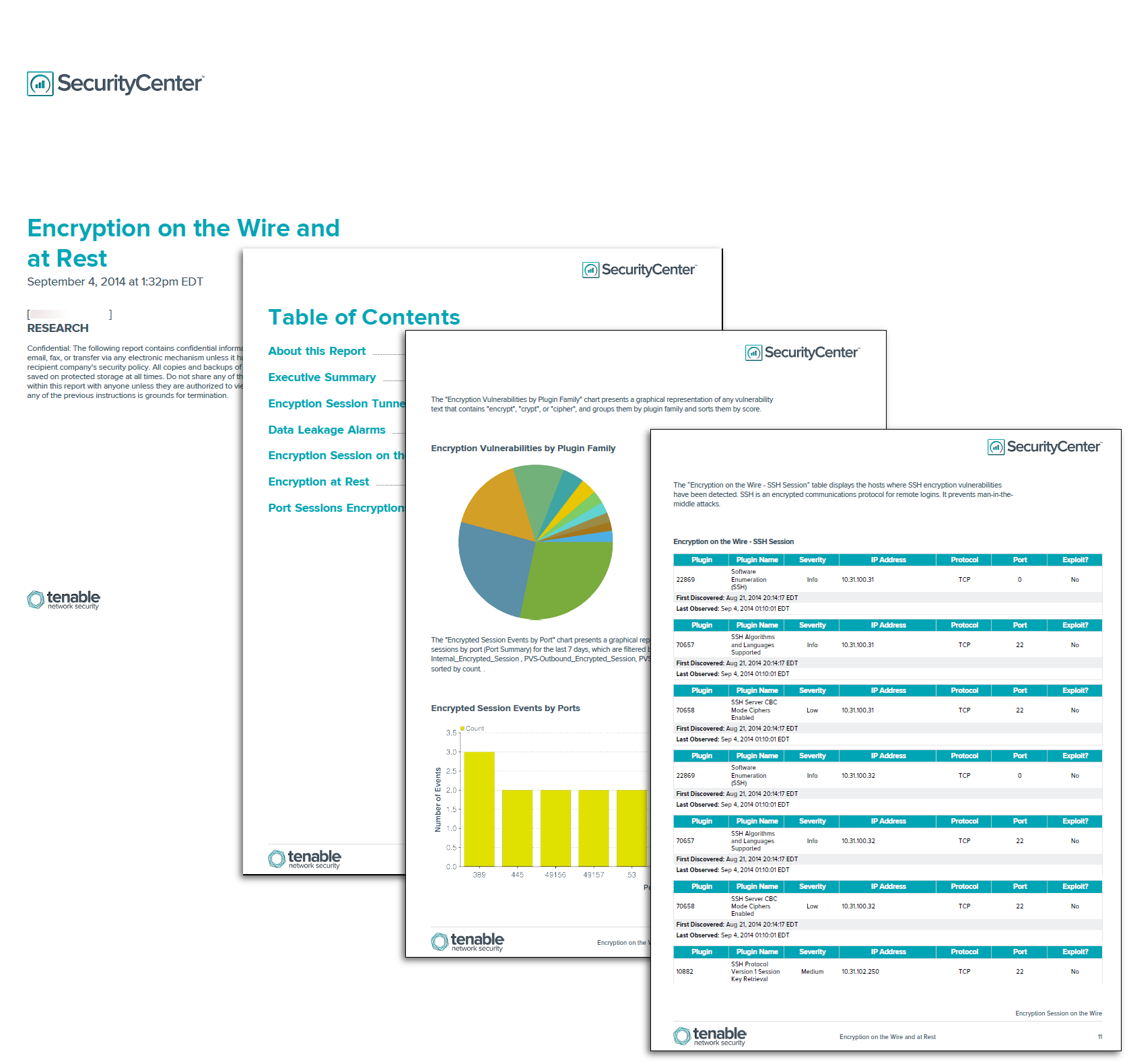
Detecting how encryption is used on the network is critical to analyzing data leakage risk. This report provides information on how encryption is used on the wire and at rest. There are six chapters for this report: Executive Summary, Encryption Session Tunnels, Data Leakage Alarms, Encryption on the Wire, Encryption at Rest, and Encryption on Port Traffic. Each chapter is separated into different methods of detecting encryption on the network. The Executive Summary chapter provides a good overview of both encryption on the wire and encryption at rest on the network. The Encryption Session Tunnels, Data Leakage Alarms, Encryption on the Wire, Encryption at Rest, and Encryption on Port Traffic chapters provide a more detailed analysis of these events and vulnerabilities.
The report is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The report can be easily located in the SecurityCenter Feed under the category Discovery & Detection. The report requirements are:
- SecurityCenter 4.8.1
- LCE 4.4
- Nessus 5.2.7
- PVS 4.0.2
Protecting sensitive, personal, and corporate data in a secure method is a hot topic in today’s world. Ensuring both encryption on the wire and at encryption at rest provides maximum security for a company. Data that is encrypted while in transit may not stay encrypted once it reaches its destination. Likewise, encrypting files before sending them over an unencrypted wire will not guarantee their security.
Encryption on the wire is the process of protecting sensitive data while being sent from one source over the network or the internet to another source. Encryption at rest is the process of encrypting hard drives or files to prevent unauthorized access.
SecurityCenter Continuous View (CV) is the market leader in providing a unique combination of vulnerability detection, compliance auditing, and reporting. SecurityCenter CV visualizes and communicates metrics that matter to the business.
Chapters:
Executive Summary: This chapter contains three charts: Trending Encryption Session for 25 Days trending chart, Encryption Vulnerabilities by Plugin Family pie chart, and Encrypted Session Events by Port bar chart. These charts will provide an overall view of trending of encryption on the wire sessions over 25 days with directional information, the types of plugin families that the encryption is being associated with, and what ports are being used with encryption for the last 7 days.
Encryption – Tunnel: This chapter provides a matrix with 11 indicators. These indicators are TLSv1, Cogent DataHub, Tor Tunnel, VPN, SQLYog, Teredo Tunnel, SOCKS, SSL Tunnel, Timbuktu Tunnel, DNS Tunnel, and SMTP Encryption Tunnel. A detailed vulnerability table list will proceed after the matrix for each indicator.
Encryption – Data Leakage: This chapter provides a matrix with 5 indicators for Generic Keys, PuTTY Keys, RSA Keys, DSA Keys, and PGP Keys. These indicators will detect if any key is passed in clear text. A detailed vulnerability table list will proceed after the matrix for each indicator.
Encryption on the Wire: This chapter provides a matrix with 12 indicators for different types of encryption on the wire including SSH, VNC, VPN, and more. These indicators provide an overview of which type of encryption vulnerabilities are being detected on the network. A detailed vulnerability table will proceed after the matrix for each indicator.
Encryption at Rest: This chapter provides a matrix with 16 indicators of the most popular encryption programs available on the market. The purpose of this matrix is to determine what encryption programs are on the network and, if there are, any vulnerability associated with them. Plugin ID 20811 enumerates software on Windows systems by sending queries to the registry. Plugin ID 22869 is a SSH enumeration plugin and uses package programs such as “rpm” to find programs installed on *nix systems. A detailed vulnerability table will proceed after the matrix for each indicator.
Encryption on Port Traffic: This chapter provides three graphical bar charts for incoming, outgoing, and internal encryption sessions by ports.