Why Third-Party Tools Are Best for Multi-Cloud CSPM

Cloud security posture management enables organizations using multiple public cloud platforms like AWS, Azure and GCP to see everything they have running and where their security risks lie. In a recent episode of the Tenable Cloud Security Coffee Break webinar series, we talked about those challenges and how Tenable Cloud Security can help. Check out the highlights of our discussion.
When it comes to managing security risk in cloud environments like Amazon’s AWS, Microsoft’s Azure and Google’s GCP, it’s often good to step back a moment and consider how these popular platforms are different from traditional on-premises infrastructure, and the unique challenges of securing them.
Public clouds offer many advantages for software teams, including APIs that can supply reams of configuration data about the environments themselves, not just about the workloads running on them. However, each cloud platform is different, has its own challenges, and requires unique expertise.
During a recent episode of Tenable’s Cloud Security Coffee Break webinar series, we sat down with Lionfish advisor and former Gartner analyst Tom Croll and Tenable Sales Engineer Paul Anderson to talk about some of these challenges and how cloud security posture management (CSPM) can help.
“You need a Rosetta Stone to compare and work with different cloud environments,” said Paul Anderson. “AWS calls it this, and Azure calls it that, and GCP calls it this other thing. It can become very complex.”
Enter CSPM tools to help with multi-cloud compliance
At its basic core, CSPM monitors the cloud control plane and provides insight into your cloud security posture. But it does a lot more today than merely show you base settings of your cloud environments.
“CSPM has evolved from being this noisy configuration monitor that tells you to tidy your room without giving you real context, to telling you the most important vulnerabilities you need to remediate,” Croll said. “We want to see the misconfigurations in each environment, the highest risks and how to remediate them.”
There are parallels with on-prem systems, but the control plane isn’t really one of them.
“We certainly can't run the equivalent of CSPM to run our data centers for us,” Croll said. “But the cloud gives us that unique API-based source in order to pull out all these configurations. We can't scan the entire security posture of our infrastructure on-prem with a single tool.”
Each cloud platform offers tools for managing CSPM, but they don’t provide much for managing other clouds on which you’re deploying workloads.
“If you're using one of those cloud service providers, you're also sort of accepting their outlook on the world, and their perspective on how the cloud should be,” Anderson said. “They're forcing the other vendors to try to fit in that paradigm, which is a recipe for risk.”
“You need a Rosetta Stone to compare and work with different cloud environments. AWS calls it this, and Azure calls it that, and GCP calls it this other thing. It can become very complex.”
—Paul Anderson, Tenable Sales Engineer
How Tenable Cloud Security can help
CSPM tools like Tenable Cloud Security enable security teams to manage security for different public clouds from a single dashboard and a single framework. Tenable Cloud Security, formerly Tenable.cs, gives you an apples-to-apples view of all your resources, regardless of the vendor, and it ranks misconfigurations according to severity, with built-in recommendations for remediating problems.
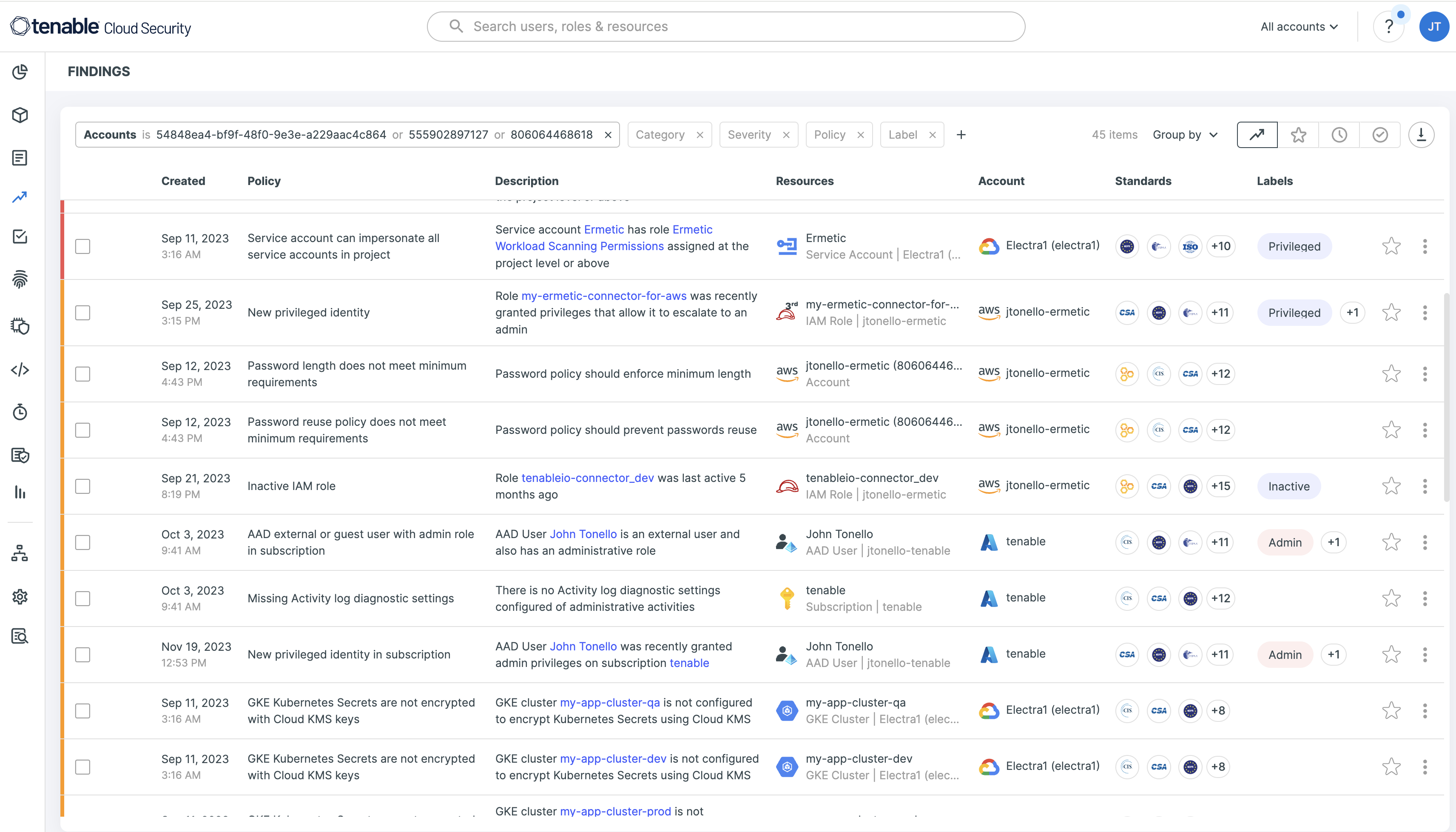
Tenable Cloud Security, which now ships as part of the Tenable One Exposure Management Platform, helps facilitate remediation by giving code snippets and detailed recommendations. It lets you quickly scan your cloud environments using more than 1,500+ built-in policies that cover dozens of common security frameworks and regulations, including those from the Center for Internet Security (CIS), the U.S. National Institute of Standards and Technology (NIST), and the EU General Data Protection Regulation (GDPR).
“In order to enable multi-cloud CSPM, I heavily advise people to go with a third party,” Croll said. “If you go with one single cloud provider, okay, start with their native tools. That's fine. But we want to have a multi cloud-enabled, or hybrid cloud-enabled security tool set and mindset. Third-party tools like Tenable Cloud Security are enabling more features to be better across multiple clouds.”
Learn more about CSPM and Tenable Cloud Security by watching this Cloud Security Coffee Break episode, and sign up to join the biweekly webinar.
Learn more
- Cloud




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success