ICS/SCADA Smart Scanning: Discover and Assess IT-Based Systems in Converged IT/OT Environments

Increasingly, operational technology (OT) environments are interconnecting with IT and adopting exploitable IT-based assets and protocols. This means OT systems are exposed to IT threats. Additionally, IT/OT convergence is expanding the cyberattack surface. Threat actors who have compromised IT networks may be able to access OT systems from the IT network. These converged environments contain a mix of IT and OT devices and systems, some of which can be easily disrupted with traditional IT active scanning techniques.
For most industrial environments, Tenable® deploys and uses continuous, passive monitoring, which is non-disruptive to OT networks. However, there are situations with converged IT/OT networks where an active scan is preferred or necessary, and where it may be difficult to segment IT and OT scan targets.
To solve this dilemma, Tenable introduces ICS/SCADA Smart Scanning. This unique capability discovers and thoroughly assesses IT-based systems (e.g., supervisory, site operational control, ERP or scheduling) in the converged environment, while reducing the risk that active scanning will disrupt OT devices if they’re inadvertently encountered during a scan.
Measuring Cyber Exposure across the entire converged IT/OT environment
With the combination of ICS/SCADA Smart Scanning and passive network monitoring, Tenable safely measures Cyber Exposure across the entire converged IT/OT environment, providing complete visibility into your cyber risks.
OT devices like programmable logic controllers (PLCs) and remote terminal units (RTUs) that monitor the activity and state of machinery (e.g., pumps, valves and motors) and environmental factors (e.g., temperature, pH and vibration) need to be inventoried and assessed for vulnerabilities to measure and manage risk to OT processes. However, these OT devices may be too sensitive to withstand the active scanning approach commonly used in IT environments. Specifically, they may be sensitive for the following reasons:
- Limited CPU power: They can be overwhelmed by too many requests because they’re designed to do only one thing at a time and may be less powerful than tablets.
- Real-time communications: The protocols involved often expect an unbroken stream of readings from a device. If they’re delayed substantially, they may have issues re-establishing communications. A full vulnerability scan probes many areas of a device very quickly, which can overly burden the limited CPU power and delay communications.
- Design tradeoffs: OT devices are designed to be resilient to power disruptions, vibrations or particles in the air. Many OT devices, especially legacy devices, have not been designed to withstand a heavy flow of network communications.
- Custom operating system and software: OT devices generally do not run widely used and widely tested operating systems, such as Windows or Linux. They may include a small HTTP server, but it is limited in feature set. When a vulnerability scanner attempts to check for SSL issues, the embedded HTTP server can crash. Since the device is only designed to do one thing at a time, this usually means the entire device reboots – causing costly downtime and potentially unsafe working conditions.
- Set it and forget it: Unlike desktops, it may be months or years before someone looks at a physical OT device. It could be operating marginally, covered in dust and close to failure. The additional load of a full vulnerability scan can cause it to reach the overload point.
Because of the risk of degradation and/or disruption, the common practice within OT environments is to avoid using active scanning approaches with OT devices. Instead, passive monitoring is used, and because passive monitoring does not interact with the sensitive devices, the devices are not impacted by it.
IT/OT convergence is resulting in many IT-based systems being deployed in the OT environment. These IT-based systems may be Windows computers running human machine interface (HMI), SCADA monitoring and historian applications. Additionally, these systems are increasingly networked to supply chain management and scheduling applications that may include databases and virtual infrastructure, which may reside in the cloud.
Typically, these IT-based systems are discovered and assessed with active scanning because active scanning can deliver much deeper insight about installed software (and related vulnerabilities), user accounts, configurations and malware.
Potential problem
Ideally, sensitive OT would be logically separated from IT-based OT systems, such as Windows computers. However, in reality, such segmentation may not exist. The potential problem is that if an existing OT device’s IP address changes or a new OT device is added, and that device is not omitted from the active scan, the scan could cause an outage.
Solution: ICS/SCADA Smart Scanning
ICS/SCADA Smart Scanning is a new attribute that can be applied to many existing scan templates. Existing scan parameters (e.g., IP ranges to be scanned/not scanned, ports, schedules and other settings) do not need to be modified.
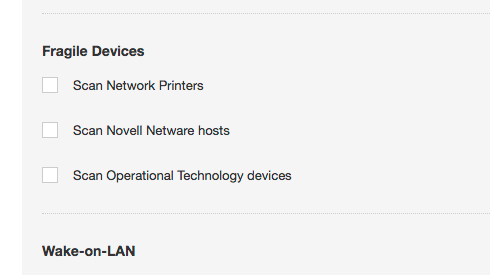
When the “Scan Operational Technology devices” box is checked, a full scan of OT devices is performed. When it is not checked, ICS/SCADA Smart Scanning takes effect.
ICS/SCADA Smart Scanning cautiously identifies OT devices and stops scanning them once they’re discovered. Here’s how it works:
- Smart Scanning pings the IP address to determine if a device is using that address.
- Smart Scanning runs probes against open known OT ports/protocols. Initially supported protocols are:
- Siemens S7
- Modbus
- BACnet
- Omron FINS
- Ethernet CIP
- 7T IGSS
- ICCP COTP
Note: ICS/SCADA Smart Scanning reduces the plugins run against devices by 90%. This eliminates the plugins that put the greatest load on the device, including HTTP and SSH testing.
- When an OT port/protocol is identified, Nessus® will report the ports that were identified to be open and the OT protocol found. Many of the protocols include INFO or QUERY commands to capture basic information about the device. If this is supported by the discovered protocol, the additional information, usually including the device type, will be recorded.
- The scan stops for that device. The plugin 109142 results show the OT device when an OT protocol was identified and normal scans of OT devices were not enabled.
- The user can use the devices listed by plugin 109142 to add the device to the “do not scan” list.
Caveat
Tenable cannot guarantee that ICS/SCADA Smart Scanning will not cause issues. Therefore, it should only be used after it has been tested with each device type in a laboratory environment and when it is known not to conflict with warranties and service agreements.

Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success