How Can We Strengthen the Cybersecurity of Critical Infrastructure? Here Are My Suggestions for CISOs, Regulators, Vendors – and All Citizens
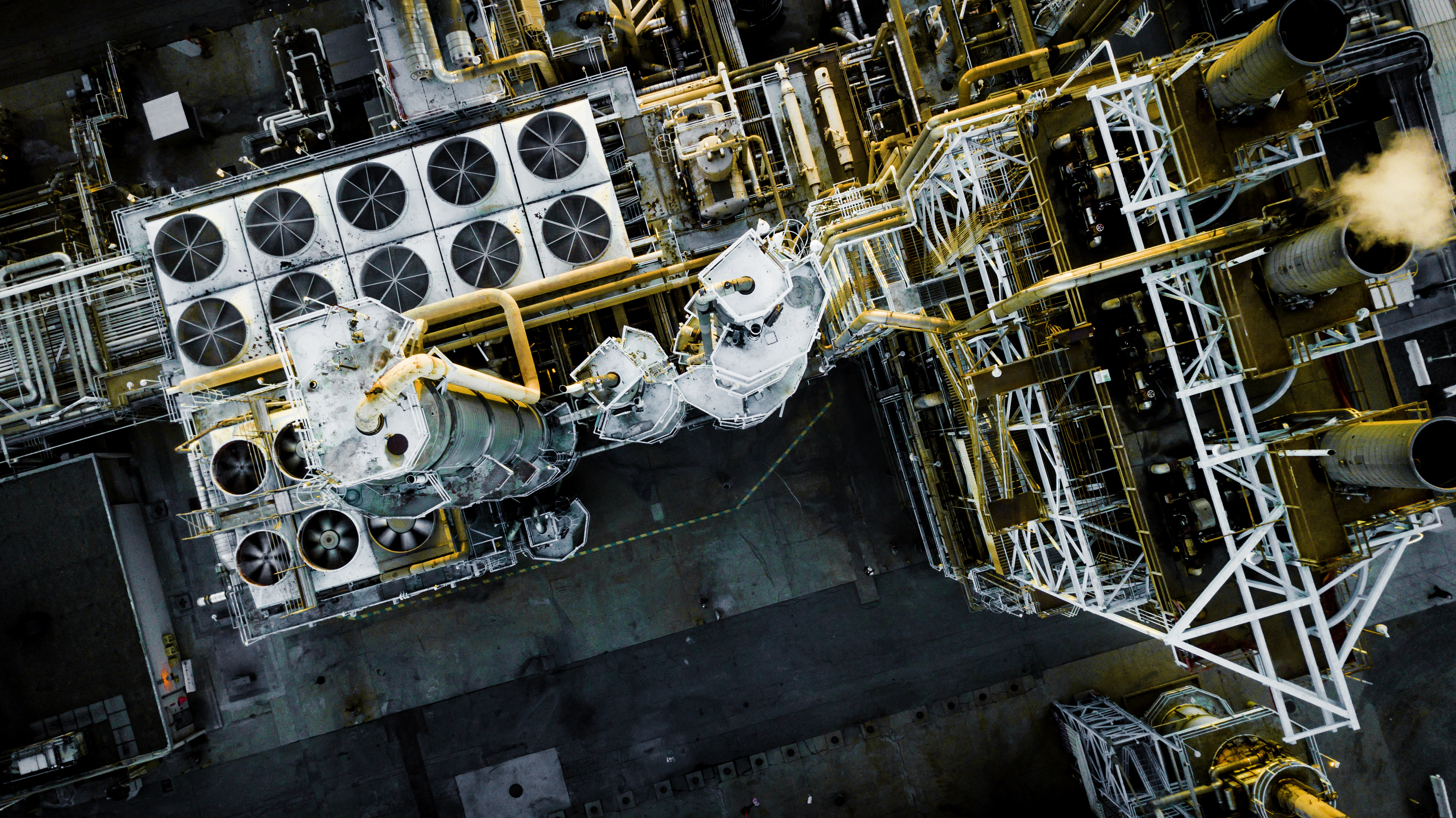
A year after the ransomware attack against the Colonial Pipeline, what can we do to further harden the IT and OT systems of power plants, fuel pipelines, water treatment plants and similar critical infrastructure facilities?
The Colonial Pipeline’s shutdown after a ransomware attack in May 2021 put a massive spotlight on the importance of protecting the IT and OT systems of critical infrastructure providers.
With major disruptions to gasoline, diesel and jet fuel distribution across multiple U.S. states lasting about a week, the incident prompted reactions at the highest levels of government and industry, including the drafting of new rules and regulations.
A year later, the initial shock of the Colonial Pipeline hack has passed, but the concern remains very much front and center. What can we do to further harden the cybersecurity of power plants, fuel pipelines, water treatment plants and similar facilities?
As someone who worked as an ICS engineer – tasked with building, maintaining and troubleshooting industrial control systems – before specializing in OT cybersecurity, the issue is near and dear to my heart.
I’ve recently participated in discussions about this matter, including in a podcast and a LinkedIn Live session, and I’d like to share here some concrete steps I’ve talked about that we can all take – the U.S. government, CISOs, cybersecurity vendors and the public at large.
CISOs, CIOs and business leaders
- CISOs, CIOs and business leaders at these critical infrastructure providers must recognize that, as the operations in these plants and facilities get increasingly digitized, more resources must naturally be allocated to cybersecurity. I’m not necessarily advocating for an increase in cybersecurity spending, but rather that it should be prioritized on the “crown jewels,” which in my mind are the OT and ICS systems.
- IT and cybersecurity leaders must also recognize that the most critical component in the cyber protection of OT systems is the people involved in it. As such, you can’t expect ICS engineers with no training or experience in cybersecurity to add on cybersecurity tasks to their regular job of keeping the plant running. You need a dedicated, experienced and trained team for OT cybersecurity.
- Once you have OT cybersecurity specialists on board, you should make sure they shadow their ICS engineers peers, so that they can get a hands-on understanding of how the facility operates, and a clearer sense of the implications that cybersecurity decisions can have on operations.
- It’s critical to have full visibility into all IT and OT systems – not just the prominent, obvious ones like enterprise applications, web servers and billing environments. Your weakest link is often a system that’s tucked away in a closet or hidden under a desk and that was once installed as a stopgap and promptly forgotten, so it’s underprotected. You must make an effort to compile a comprehensive inventory of all your systems, and gain an understanding of the role each one plays.
- Fix or mitigate your vulnerabilities, because they’re the low-hanging fruit that ransomware operators look for, and ICS environments are particularly at risk due to the prevalence of legacy software in them.
Vendors
- ICS vendors must make their wares more secure. Many legacy ICS systems are insecure by design. They should be re-designed from the ground up with default security features and capabilities, such as secure protocols and approved mechanisms for authenticated firmware updates.
- OT cybersecurity vendors must recognize that the ultimate goal of the technology they market is to keep critical infrastructure safe for the benefit of everybody in our society. As such, they should compete on the merits of their products, not on imposing proprietary technology that locks customers into their vendor ecosystem. Equally as important is to have a spirit of cooperation and open communication, despite their competitive differences, so that they can collaborate on advancing OT cybersecurity technology that better protects critical infrastructure. That’s why at Tenable we helped launch the Operational Technology Cybersecurity Coalition, where we advocate for the development of vendor-neutral, interoperable, standards-based cybersecurity solutions.
The U.S. government
- It’s the role of the government to issue rules and regulations to ensure that a baseline standard of care is applied to safeguard the OT and IT systems of critical infrastructure providers. To be truly effective, these requirements should be outcome oriented – meaning, they should outline goals and achievements that should be attained. They’ll be less impactful if they’re overly detailed and prescriptive from a technical standpoint, because the government’s regulatory wheel typically turns slowly, and the mandates will soon become outdated, as the technology changes quickly.
- The government does a great job of designing and carrying out exercises for its agencies to practice responses to crisis situations. It’d be great if the government shared its OT cybersecurity exercises with the private sector, which in turn could help the government better understand in more detail the wide variety of ICS deployments in operation across the country.
Regular citizens
- The cybersecurity of our critical infrastructure should be everyone’s concern – even the large majority of people who aren’t in the first three buckets I addressed above. Here’s what you can do: Let your voice be heard. Get involved. Phone your state and local representatives. Participate in public forums where decision makers take feedback from residents. Be ready to have meaningful conversations with them. This isn’t someone else’s problem. It affects all of us.
If you’re interested in learning more about these topics, I invite you to listen to my recent conversations on the podcast The State of OT Security, a Year Since Colonial Pipeline with my Tenable colleague Dan Raywood, and on the LinkedIn Live session Colonial Pipeline One Year Later: What Have (and Haven’t) We Learned? with CNN cybersecurity reporter Sean Lyngaas.
You may also be interested in tuning into a transport-focused OT webinar we’re hosting on June 15 at 2 pm ET – Unpacking Some of the Most Common Cybersecurity Challenges Facing Your Transportation-Sector Business – with panelists from the U.S. Transportation Security Administration (TSA) and two of our partners. Sign up for this webinar today!
- OT Security


