Adobe Patches Incomplete Fix for NTLM Credential Leaking Bug (CVE-2018-15979)

Researchers have reported an incomplete fix for CVE-2018-4993, an NTLM credential leaking vulnerability that was supposed to be patched in May 2018. Adobe has now released a complete fix.
背景說明
On November 13, Adobe published its monthly security bulletins as part of its monthly release cycle in conjunction with Microsoft’s Patch Tuesday. The November security bulletins include a fix for a vulnerability that was believed to have been patched in May 2018’s security bulletins. However, security researchers at EdgeSpot discovered that the May 2018 fix was incomplete.
Vulnerability details
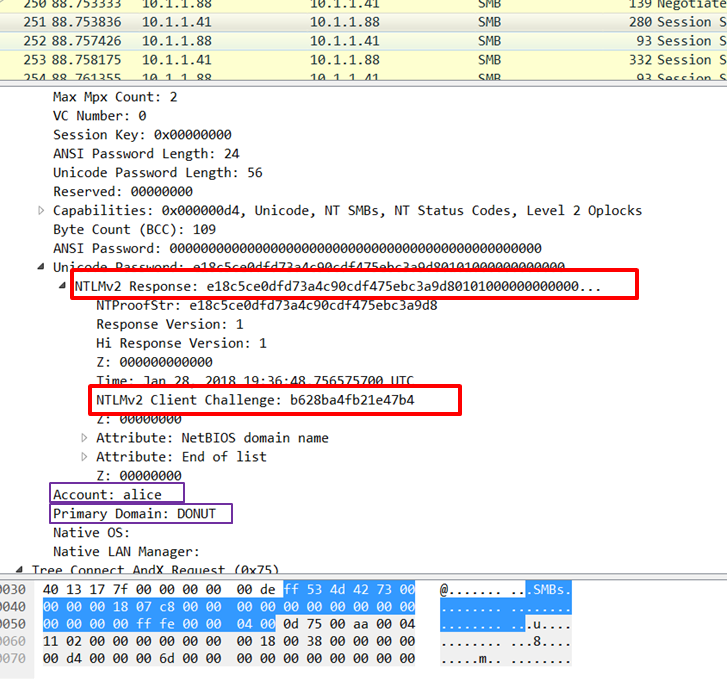
Researchers at Check Point Software Technologies originally reported this vulnerability to Adobe earlier in 2018. The vulnerability, CVE-2018-4993, is an information disclosure bug that leaks NT LAN Manager (NTLM) credentials through a feature of Portable Document Files (PDFs) that allows embedding remote documents and files. These credentials can be leaked when an attacker sends a specially crafted PDF file to a victim and includes the NTLM hash and challenge along with user and domain details.
原文: Checkpoint
Adobe reportedly patched this vulnerability in May 2018 as part of its security bulletin, APSB18-09. However, researchers at EdgeSpot, makers of an exploit detection service, determined that the May 2018 patch for CVE-2018-4993 was incomplete. The researchers examined two malicious PDF files (here and here) submitted to VirusTotal in May 2018 and determined the vulnerability still works using the latest version of Adobe Reader.
It appears that when Adobe issued their patch for this vulnerability in May 2018, it only patched one of two action types required when embedding remote documents and files. The two action types are:
- GoToR (GoToRemote)
- GoToE (GoToEmbedded)
EdgeSpot researchers say Adobe only patched GoToR and not GoToE based on the malicious PDF files they examined, both of which contained the GoToE action type. After reporting this to Adobe in early November, it was identified as a new CVE, CVE-2018-15979 and patched in Adobe’s November security bulletins.
Urgently required actions
Customers and users are strongly advised to upgrade to the latest versions of Adobe Acrobat and Acrobat Reader, which can be found here.
找出受影響的系統
A list of Nessus plugins to identify this vulnerability can be found here.
取得更多資訊
- NTLM Credentials Theft via PDF Files
- The case of the unpatched variant of the PDF NTLM leaking vulnerability CVE-2018-4993
- Adobe Security Bulletin (APSB18-40)
- Adobe Security Bulletin (APSB18-09)
Learn more about Tenable, the first Cyber Exposure platform for holistic management of your modern attack surface. Get a free 60-day trial of Tenable.io Vulnerability Management.
- Vulnerability Management

