by Megan Daudelin
April 18, 2017
The information published by the Shadow Brokers hacking group identified many major vulnerabilities in common operating systems and services. Failure to remediate impacted systems could leave the network susceptible to intrusion or exploitation. By leveraging the vulnerability data gathered by Tenable Nessus, Tenable SecurityCenter is able to provide detailed insight into the hosts on the network that are most vulnerable to the intrusion methods most recently publicized by Shadow Brokers.
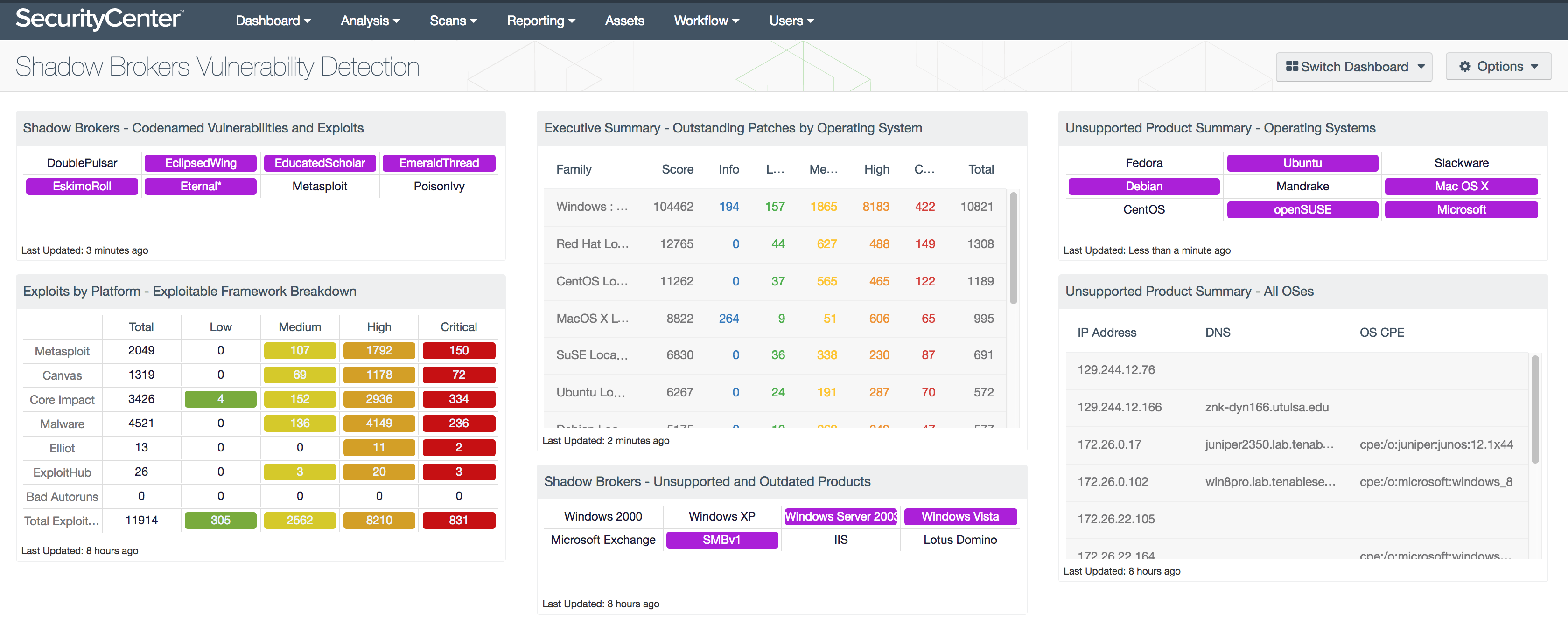
This dashboard displays detailed information about the vulnerabilities and exploits identified by the Shadow Brokers hacking group. In addition to vulnerabilities being tracked by codename, unsupported and outdated products are targeted for detection. The vulnerabilities publicized by Shadow Brokers specifically target unsupported and outdated operating systems and services, so patching or upgrading hosts on the network is key to remediation and defense.
The components in this dashboard leverage data gathered by active vulnerability scanning with Nessus. The data collected is filtered to provide insight into the vulnerabilities related to those published by the Shadow Brokers. Matrices identify the presence of specific vulnerabilities, as well as outdated or unsupported products. Tables are filtered to include lists of unsupported or unpatched operating systems. Security teams can use all of the information provided by this dashboard in order to effectively prioritize the hosts in their network for remediation in response to the vulnerabilities made public by the Shadow Brokers hacking group.
This dashboard is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Threat Detection & Vulnerability Assessments. The dashboard requirements are:
- SecurityCenter 5.4.5
- Nessus 6.10.5
Tenable SecurityCenter is the market-defining continuous network monitoring solution, and can assist in securing an organization’s internal network and effectively remediating new vulnerabilities. SecurityCenter is continuously updated with information about advanced threats, zero-day vulnerabilities and new regulatory compliance data. Active scanning periodically examines systems to determine vulnerabilities and compliance concerns. Agent scanning enables scanning and detection of vulnerabilities on transient and isolated devices. SecurityCenter provides an organization with the most comprehensive view of the network and the intelligence needed to support effective vulnerability remediation efforts.
The following components are included in this dashboard:
- Shadow Brokers - Codenamed Vulnerabilities and Exploits: This matrix displays the codenamed vulnerabilities and associated exploits published by the Shadow Brokers hacking group.
- Exploits by Platform - Exploitable Framework Breakdown: This matrix displays the counts of vulnerabilities by exploit framework and severity.
- Executive Summary - Outstanding Patches by Operating System: This component is a table with counts of vulnerabilities based on the OS local security check plugins.
- Shadow Brokers - Unsupported and Outdated Products: This matrix specifically identifies the unsupported or outdated operating systems or services known to be particularly vulnerable to exploitation.
- Unsupported Product Summary - Operating Systems: This indicator matrix reports on operating systems that are no longer supported.
- Unsupported Product Summary - All OSes: This table lists the hosts determined to be running unsupported operating systems.