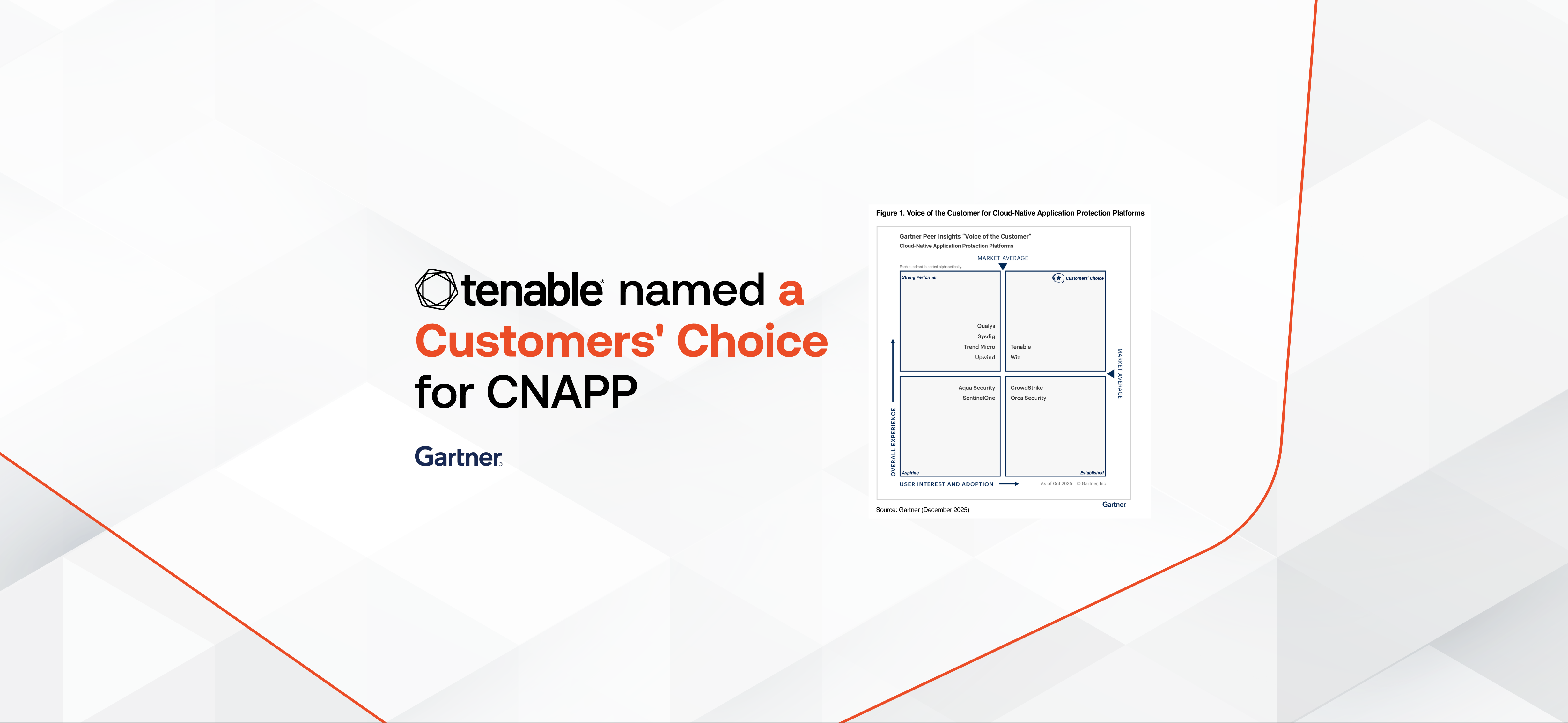
Tenable Is a Gartner® Peer Insights™ Customers’ Choice for Cloud-Native Application Protection Platforms

網路安全概要: Predictions for 2026: AI Attack Acceleration, Automated Remediation, Custom-Made AI Security Tools, Machine Identity Threats, and More








感謝訂閱!
Form ID: 3971
Form Name: blog-subscribe
Form Class: c-form u-p--0 c-form--light c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: blog-subscribe-form-wrapper
Confirmation Class: blog-subscribe-confirmform-modal
Simulate Success