Microsoft’s July 2020 Patch Tuesday Addresses 123 CVEs Including Wormable Windows DNS Server RCE (CVE-2020-1350) (SIGRed)
Microsoft addresses 123 CVEs, including CVE-2020-1350, a wormable remote code execution vulnerability in Windows DNS Server dubbed “SIGRed.”
For the fifth month in a row, Microsoft has patched over 100 CVEs, addressing 123 CVEs in the July 2020 Patch Tuesday release. Included this month is a highly critical remote code execution (RCE) vulnerability in Windows DNS Server (CVE-2020-1350). The updates this month include patches for Microsoft Windows, Microsoft Edge, Microsoft ChakraCore, Internet Explorer, Microsoft Office and Microsoft Office Services and Web Apps, Windows Defender, Skype for Business, Visual Studio, Microsoft OneDrive, Open Source Software, .NET Framework and Azure DevOps.
CVE-2020-1350 | Windows DNS Server Remote Code Execution Vulnerability
CVE-2020-1350 is an RCE vulnerability within the Windows Domain Name System (DNS) server due to an issue in how the DNS server parses requests. The vulnerability has a 10.0 CVSSv3 score, the highest possible rating. The flaw has existed for 17 years, affecting Windows Server versions from 2003 to 2019, and was discovered by Sagi Tzadik and Eyal Itkin from Check Point Research who have dubbed this vulnerability “SIGRed.” Microsoft acknowledges that this vulnerability is “wormable,” or potentially spreadable via malware between affected hosts in a network without any user interaction.
DNS is a core networking component and any compromise of a DNS server could have a severe impact within an organization. This vulnerability received a patch for Windows Server 2008, which went end of life in January 2020, underscoring the severity of this issue. Microsoft recommends patching this vulnerability as soon as possible and offers a workaround for those that cannot immediately patch. The workaround, described in KB4569509, works by setting the maximum length of a DNS message over TCP to 62,580 bytes (0xFF00): this prevents a Windows DNS server from resolving hostnames when the DNS response from an upstream server exceeds this maximum threshold.
CVE-2020-1032, CVE-2020-1036, CVE-2020-1040, CVE-2020-1041, CVE-2020-1042, CVE-2020-1043 | Hyper-V RemoteFX vGPU Remote Code Execution Vulnerability
CVE-2020-1032, CVE-2020-1036, CVE-2020-1040, CVE-2020-1041, CVE-2020-1042, and CVE-2020-1043 are RCE vulnerabilities in Hyper-V RemoteFX vGPU due to the host server not properly validating input from guest operating systems. If an attacker executes malicious code on a guest operating system, they could attack third-party video drivers on the Hyper-V host, which could result in the host operating system executing malicious code.
The related patches do not fix this vulnerability. Instead, these patches disable RemoteFX, a visual enhancement suite provided by Microsoft to improve the video quality of RDP sessions. Without RemoteFX, visual display tasks during RDP sessions will likely be handled by the host CPU, rather than the GPU on Server 2012 and older hosts. Microsoft Server 2016 and newer have Discrete Device Assignment (DDA) which handles these tasks, as RemoteFX was deprecated in Windows Server 2019.
CVE-2020-1400, CVE-2020-1401 and CVE-2020-1407 | Jet Database Engine Remote Code Execution Vulnerability
CVE-2020-1400, CVE-2020-1401 and CVE-2020-1407 are RCE vulnerabilities that exist when Windows Jet Database Engine improperly handles objects in memory. Successful exploitation of these vulnerabilities would allow an attacker to execute arbitrary code on an affected system. To exploit this vulnerability, an attacker must convince a victim to open a specially crafted file or visit a malicious website.
CVE-2020-1446 | Microsoft Word Remote Code Execution Vulnerability
CVE-2020-1446 is an RCE vulnerability that exists in Microsoft Word when it fails to handle objects in memory. Successful exploitation of this vulnerability would allow an attacker to perform actions in the context of the current user, with the user’s rights and permissions. Exploitation of this vulnerability requires an attacker to send a specially crafted file to a victim, or to convince a user to visit a crafted website hosting a malicious file which the user must open with a vulnerable version of Microsoft Word.
CVE-2020-1374 | Remote Desktop Client Remote Code Execution Vulnerability
CVE-2020-1374 is an RCE vulnerability in the Windows Remote Desktop Client caused by malicious code running on a remote server. When a client connects to an infected server, they become susceptible to an RCE attack. An attacker would either need to compromise a trusted server, or use some other method, like a Man in the Middle (MitM) style attack, to intercept a user’s RDP attempts and redirect them to a malicious server.
CVE-2020-1481 | Visual Studio Code ESLint Extension Remote Code Execution Vulnerability
CVE-2020-1481 is an RCE vulnerability that exists in the ESLint extension for Visual Studio Code when it validates source code after opening a project. Successful exploitation of this vulnerability would allow an attacker to execute arbitrary code in the context of the current user, with the same rights and permissions.
Exploitation of this vulnerability would require an attacker to convince a victim to clone a repository that contains malicious executable code and open it with a vulnerable version of Visual Studio Code. If the target is an Admin user, the code could be configured to create accounts with admin rights and permissions, install malicious programs and view, alter or delete data.
CVE-2020-1381 and CVE-2020-1382| Windows Graphics Component Elevation of Privilege Vulnerability
CVE-2020-1381 and CVE-2020-1382 are elevation of privilege vulnerabilities that exist when the Windows Graphic Component improperly handles objects in memory. Successful exploitation of these vulnerabilities would allow an attacker to run processes in an elevated context. Exploitation of these vulnerabilities would require an attacker to log onto a vulnerable system and execute a specially crafted application to take control of the system.
CVE-2020-1403 | VBScript Remote Code Execution Vulnerability
CVE-2020-1403 is an RCE vulnerability in the mishandling of memory objects in the VBScript engine. An attacker would have to convince a user to execute malicious code, either through phishing or convincing a user to visit a malicious website, where the user would download and execute a crafted file. Once the user executes the malicious code, commands can then be executed against the local host as the current user.
Tenable solutions
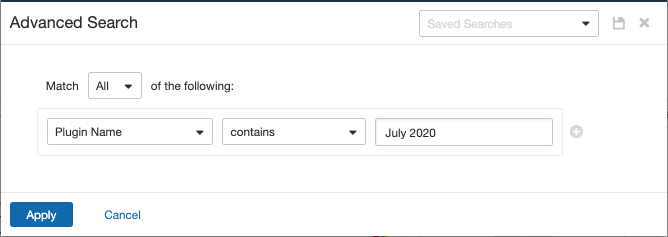
Users can create scans that focus specifically on our Patch Tuesday plugins. From a new advanced scan, in the plugins tab, set an advanced filter for Plugin Name contains July 2020.
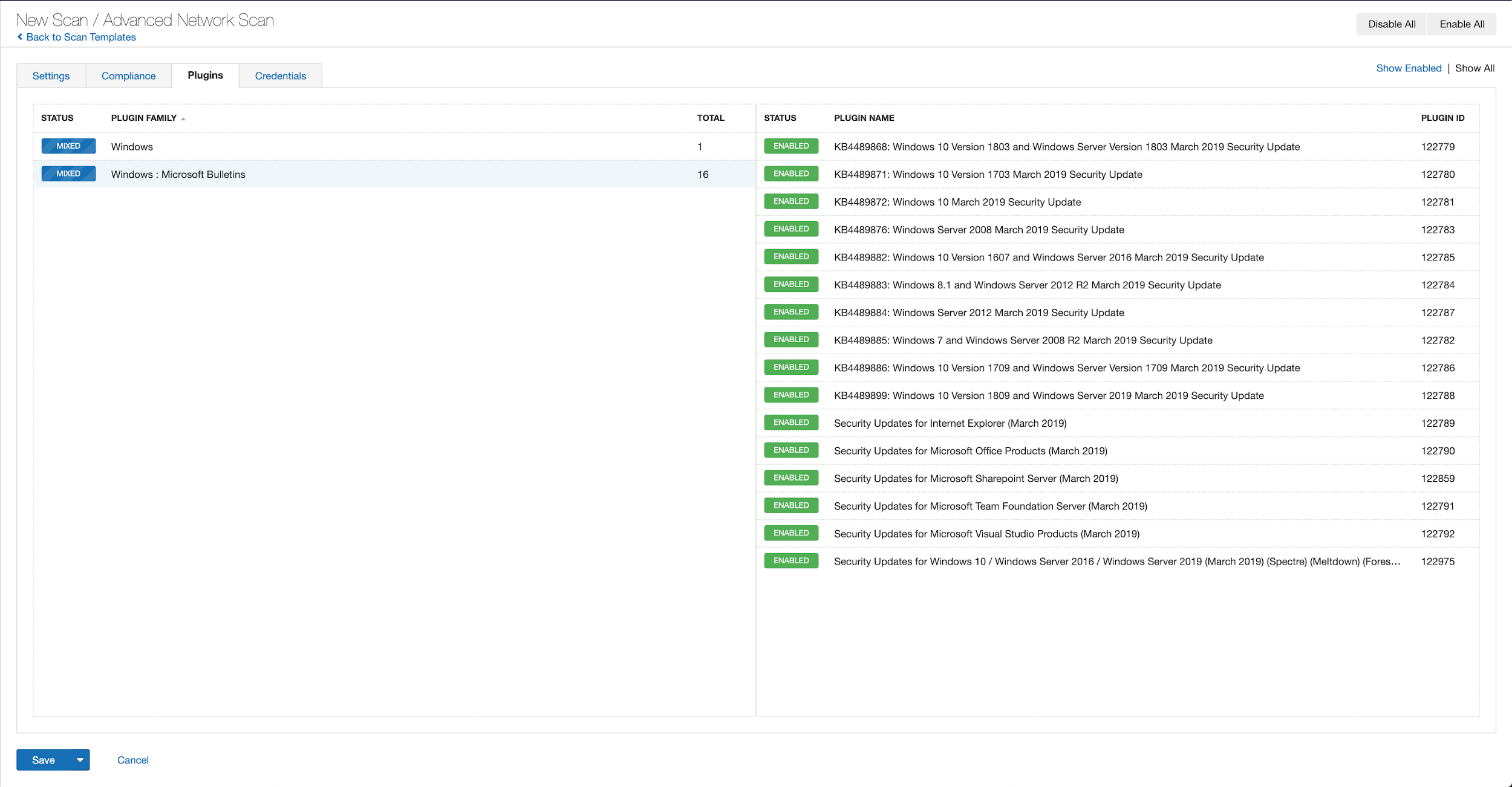
With that filter set, click the plugin families to the left and enable each plugin that appears on the right side. Note: If your families on the left say Enabled, then all the plugins in that family are set. Disable the whole family before selecting the individual plugins for this scan. Here’s an example from Tenable.io:
A list of all the plugins released for Tenable’s July 2020 Patch Tuesday update can be found here. As always, we recommend patching systems as soon as possible and regularly scanning your environment to identify those systems yet to be patched.
Get more information
- Microsoft's July 2020 Security Updates
- Tenable plugins for Microsoft July 2020 Patch Tuesday Security Updates
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable, the first Cyber Exposure platform for holistic management of your modern attack surface.
Get a free 30-day trial of Tenable.io Vulnerability Management.
- Vulnerability Management
