CVE-2021-21972: VMware vCenter Server Remote Code Execution Vulnerability
Proof-of-concept exploit scripts for a critical remote code execution flaw, along with mass scanning activity, indicate that organizations should apply vCenter Server patches immediately.
Update May 26: The Proof of concept section has been updated to reflect the publication of a proof-of-concept (PoC) for CVE-2021-21974.
Background
On February 23, VMware released a security advisory (VMSA-2021-0002) to address two vulnerabilities in vCenter Server, a centralized management software for VMware vSphere systems, as well as a vulnerability in the VMWare ESXi hypervisor.
| CVE | Affected Product | CVSSv3 |
|---|---|---|
| CVE-2021-21972 | vCenter Server | 9.8 |
| CVE-2021-21973 | vCenter Server | 5.3 |
| CVE-2021-21974 | ESXi | 8.8 |
The most notable vulnerability disclosed as part of this advisory is CVE-2021-21972, a critical remote code execution (RCE) flaw in vCenter Server. The vulnerability was discovered and disclosed to VMware by Mikhail Klyuchnikov, a security researcher at Positive Technologies.
In recent years, Klyuchnikov has been credited with discovering and disclosing critical vulnerabilities that were later exploited by attackers in the wild. These include CVE-2019-19781, a critical vulnerability in Citrix Application Delivery Controller (ADC) and Gateway, and CVE-2020-5902, a critical vulnerability in F5 BIG-IP.
Analysis
CVE-2021-21972 is an unauthorized file upload vulnerability in vCenter Server. The issue stems from a lack of authentication in the vRealize Operations vCenter Plugin. It received a critical CVSSv3 score of 9.8 out of 10.0. An unauthenticated, remote attacker could exploit this vulnerability by uploading a specially crafted file to a vulnerable vCenter Server endpoint that is publicly accessible over port 443. Successful exploitation of this vulnerability would result in an attacker gaining unrestricted RCE privileges in the underlying operating system of the vCenter Server.
Klyuchnikov published a blog post detailing his discovery of the vulnerability, as well as two separate paths to achieve RCE. For Windows systems, an attacker could upload a specially crafted .jsp file in order to gain SYSTEM privileges on the underlying operating system. For Linux systems, an attacker would need to generate and upload a public key to the server’s authorized_keys path and then connect to the vulnerable server via SSH.
Default installations of vCenter Server are vulnerable
Despite the fact that this vulnerability stems from the vRealize Operations vCenter Plugin, the VMware advisory confirms that this plugin is included “in all default installations” of vCenter Server. This means that the vulnerable endpoint is available irrespective of the presence of vRealize Operations.
Over 6,700 vCenter Server systems are publicly accessible
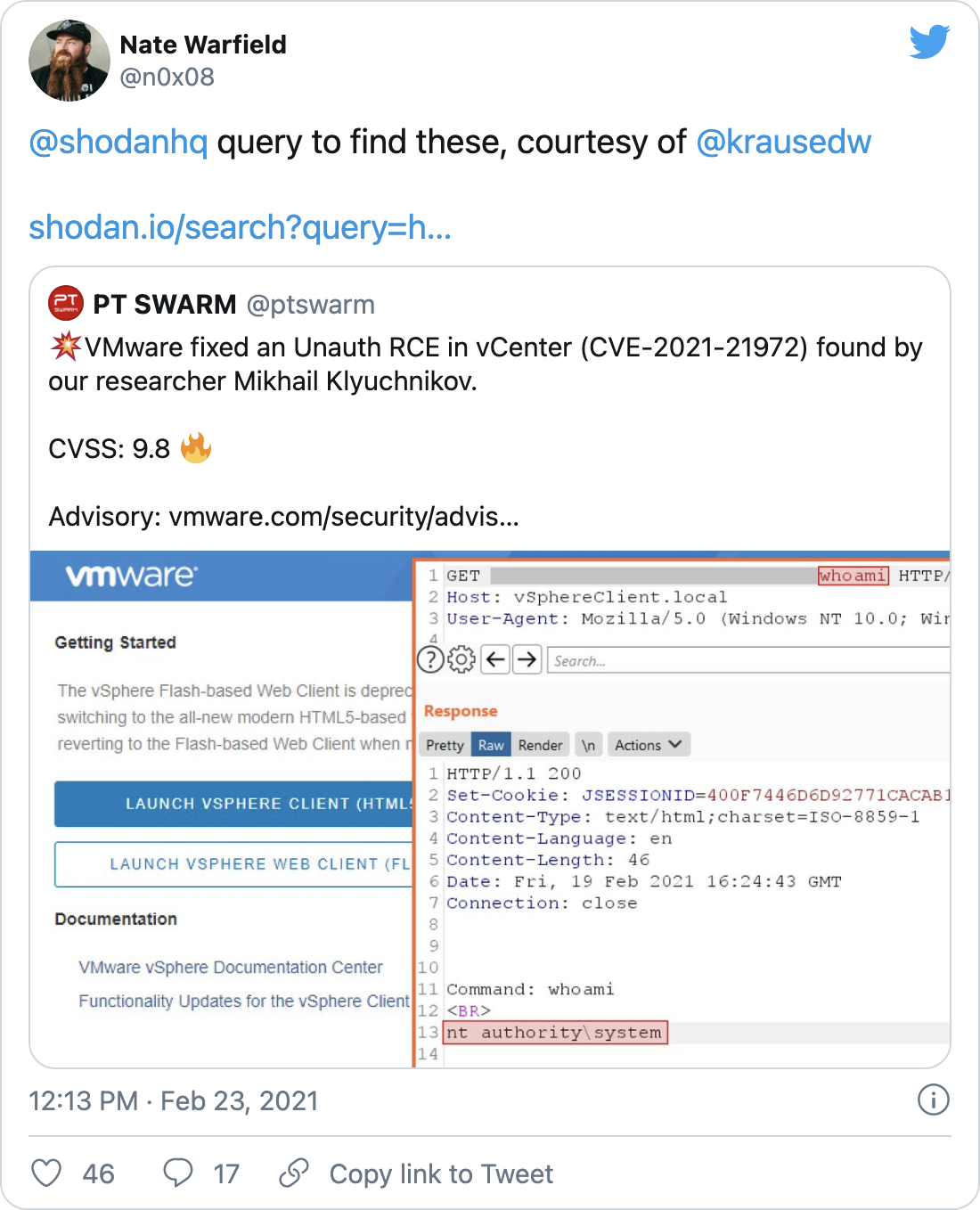
According to a Shodan search query from David Krause, a threat intelligence engineer, there are currently over 6,700 vCenter Server systems that are publicly accessible.
Mass scanning activity for CVE-2021-21972 detected within one day
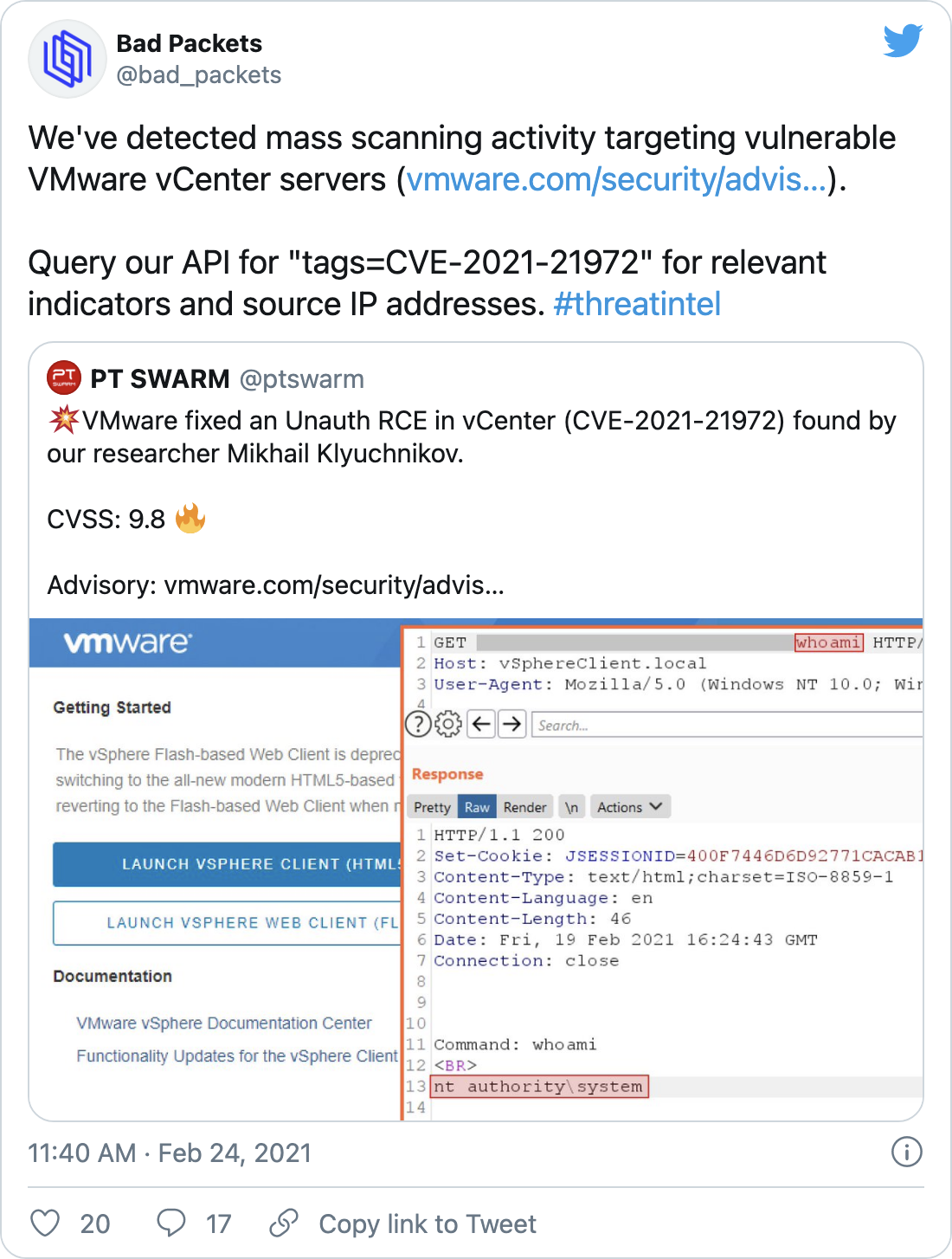
On February 24, just one day after VMware published their advisory, Troy Mursch, chief research officer at Bad Packets, tweeted that mass scanning activity has been detected searching for vulnerable vCenter servers.
Other vulnerabilities addressed in VMware Advisory
In addition to CVE-2021-21972, VMware addressed CVE-2021-21973, a Server Side Request Forgery (SSRF) vulnerability in vCenter Server that was also discovered by Klyuchnikov, as well as CVE-2021-21974, a heap overflow vulnerability in VMware ESXi that was discovered by Lucas Leong.
Proof of concept
At the time this blog post was published, there were at least four proof-of-concept exploit scripts available on GitHub, including one that is configurable for both Windows and Linux targets:
- NS-Sp4ce/CVE-2021-21972
- QmF0c3UK/CVE-2021-21972-vCenter-6.5-7.0-RCE-POC
- horizon3ai/CVE-2021-21972
- yaunsky/CVE-2021-21972
On May 25, researcher Johnny Yu published a PoC for CVE-2021-21974 to GitHub along with a blog post on how it was developed.
Solution
On February 23, VMware released the following updates for vCenter Server to address CVE-2021-21972 and CVE-2021-21973:
| Affected Product Version | Fixed Version |
|---|---|
| vCenter Server 6.5 | 6.5 U3n |
| vCenter Server 6.7 | 6.7 U3l |
| vCenter Server 7.0 | 7.0 U1c |
Additionally, the following VMware Cloud Foundation platform versions are also impacted by these vulnerabilities:
| Affected Product Version | Fixed Version |
|---|---|
| Cloud Foundation 3.x | 3.10.1.2 |
| Cloud Foundation 4.x | 4.2 |
If upgrading is not feasible at this time, VMware has provided workaround instructions for CVE-2021-21972 and CVE-2021-21973 that involve a change to the compatibility matrix file and setting the vRealize Operations vCenter Plugin to incompatible.
Please note that this should only be used as a temporary workaround until upgrading is feasible.
Identifying affected systems
A list of Tenable plugins to identify these vulnerabilities will appear here as they’re released.
Get more information
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable, the first Cyber Exposure platform for holistic management of your modern attack surface.
Get a free 30-day trial of Tenable.io Vulnerability Management.
Learn more
- Vulnerability Management




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success