by Noah Cutler
When assessing an organization’s security posture, one of the first steps is to identify operating system (OS) running across all network assets. To track assets, many organizations perform discovery scans using active scanning methods. Unfortunately, this method fails to account for vulnerabilities on transient assets such as laptops, mobile devices, and virtual machines. This dashboard leverages information collected from Tenable Nessus Network Monitor on passively detected operating systems within the network, which can assist security teams in measuring and reducing cyber risk.
Tenable.sc leverages the Passive OS Detection plugin which uses several fingerprinting methods to discover operating systems on a given network. By understanding what operating systems are present on the network, the operations team can easily manage vulnerability patches and track hosts. Maintaining an up-to-date list of known hosts, which serves as a valuable baseline for measuring and reducing cyber risk.
The Passive OS Detection dashboard provides operating system information detected passively by the Tenable Nessus Network Monitor. The plugin uses multiple passive fingerprinting techniques to identify operating systems. These criteria include methods from TCP header analysis to application-level identification. Analysts can use this data to track systems running outdated operating systems that need to be upgraded or systems that are at end of life. Results may also include data on detected portable storage devices, network infrastructure devices, and virtual platforms on the network. Results will include a confidence level score out 100. The accuracy of the OS fingerprinting should improve as more traffic is observed.
This dashboard is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Monitoring. The dashboard requirements are:
- Tenable.sc 5.5.0
- Nessus Network Monitor 5.9.0
Tenable's Tenable.sc Continuous View (CV) provides continuous network monitoring, vulnerability identification and security monitoring. Tenable.sc eliminates blind spots by detecting missing patches, misconfigurations, lapsed defenses, and network intruders. Nessus Network Monitor, which is used by Tenable.sc, provides deep packet inspection to continuously discover and track users, applications, cloud infrastructure, trust relationships, and vulnerabilities. This deep packet analysis gives you the tools you need to take control of your network’s Cyber Exposure.
The included components are listed below:
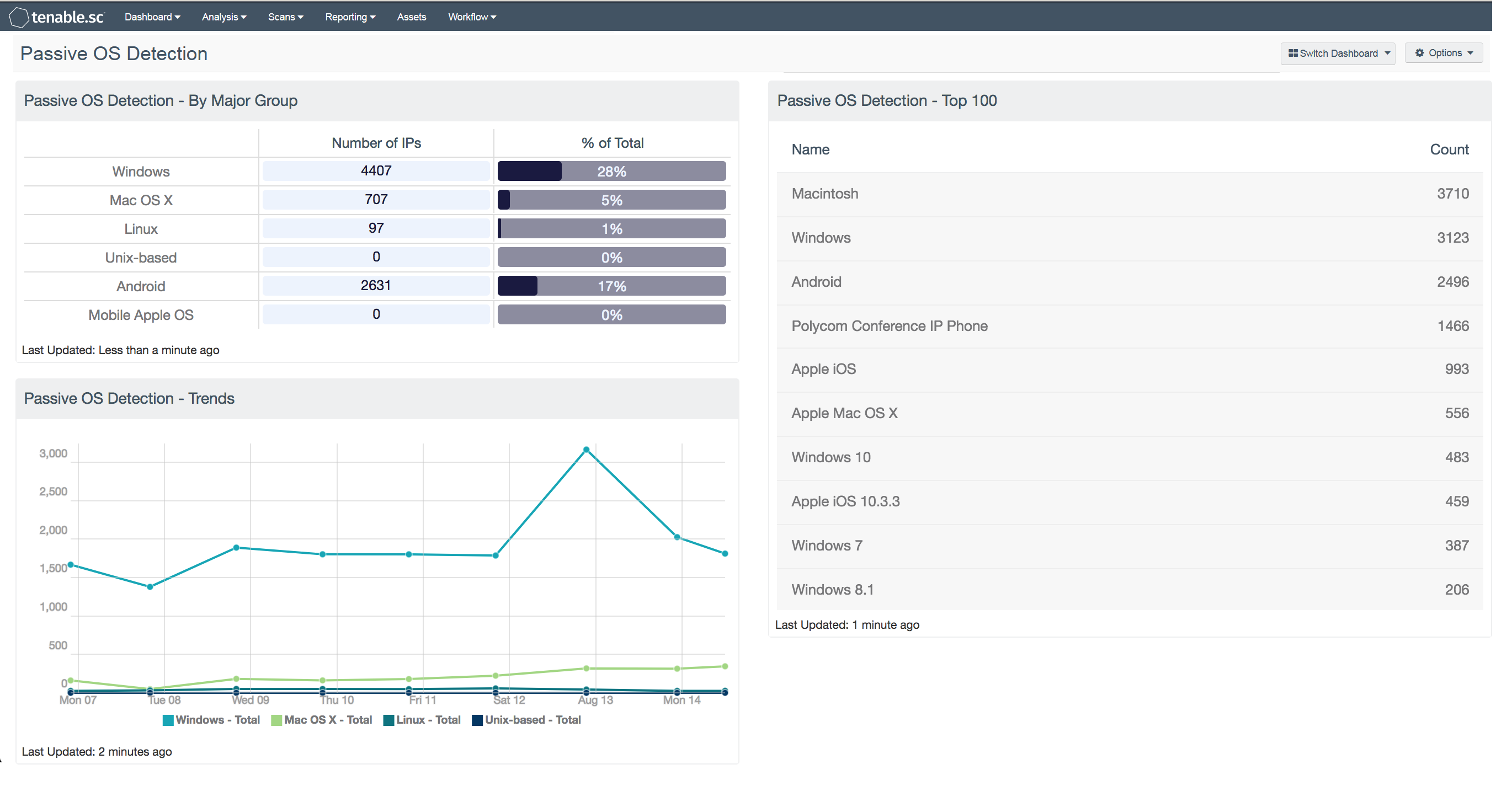
Passive OS Detection - By Major Group - This component presents the number of hosts with detected operating systems in the specified major groups. For each group, the percentage of total detections is also displayed.
Passive OS Detection - Top 100 - This table presents the top 100 most common operating systems detected on the network, with host counts. The confidence level and method of detecting the operating system are also displayed.
Passive OS Detection - Trends - The Passive OS Detection – Trends chart presents a 7-day trend history of OS detections. Each line represents the presence of a major operating system type on the network. Each individual data point represents an accumulation of OS detection information collected by Nessus Network Monitor over a period of 24 hours. These data points are presented over a range of one week.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success