Tenable CIEM
雲端基礎架構與權限管理
在公用雲端中,身分與權限是您雲端基礎架構最大的風險。只要有一個身芬和存取管理 (IAM) 錯誤設定,就有可能讓不法之徒存取您整個雲端環境。Tenable CIEM 能解決這些挑戰,讓您建置最低權限模式,並以安全的方式擴大雲端的採用。
申請示範
Secure Your Cloud From Attackers Exploiting Identities, Overly-Permissive Access, and Excessive Permissions
Exploited identities cause almost all data breaches. Bad actors target mismanaged IAM privileges to access your sensitive data. Unfortunately, almost all cloud permissions are over-privileged — an accident waiting to happen. Cloud complexity — including thousands of microservices that need access to resources and layers of policies that change frequently — makes understanding access risk and permissions difficult.
Leading analysts recommend that enterprises automate entitlement management and least privilege as a key part of their cloud strategy. Tenable CIEM does just that.
取得 Tenable 領先業界的雲端身分與權限安全解決方案
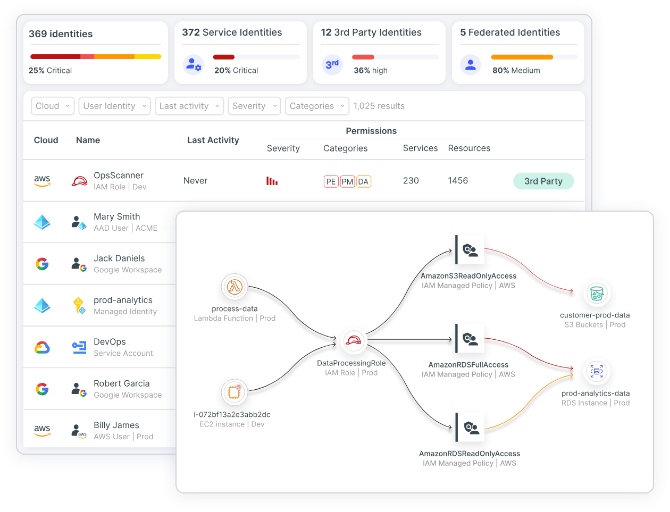
Tenable CIEM offers the most comprehensive solution for securely managing human and service identities in your cloud environment. Visualize all identities and entitlements, using automated analysis to reveal and prioritize risks, including excessive permissions and toxic combinations, accurately and in context. Gather fine-grained insight into the access needed to perform a task, remediate risk using automated workflows, shift left on least privilege and investigate suspicious behavior.
With Tenable CIEM, you can answer critical identity-related cloud security questions, such as:
- 在雲端中,哪些人可以存取哪些資源?
- 我們最大的風險在哪裡?
- 我要採取哪些行動來進行修復?
- 我要如何確保雲端中的合規性?
“ [Tenable Cloud Security] goes beyond permissions visibility to reveal IAM risk context that informs our busy DevOps team, facilitating their efforts in mitigating risk and minimizing disruption.”Aidoc 共同創辦人技研發部門副總裁 Guy Reiner
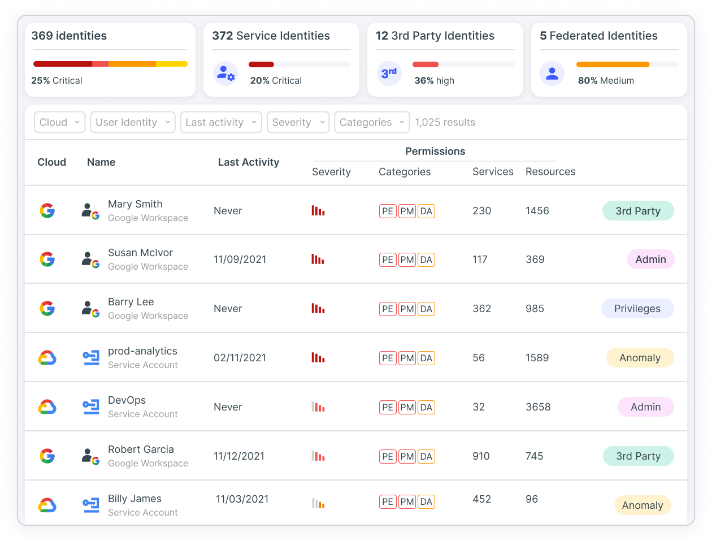
多重雲端資產管理與全端風險評估
Continuously discover and visualize a full inventory of all cloud identities, entitlements, resources and configurations in your cloud environment, including IAM, federated and third-party users. Tenable CIEM applies full-stack analysis that evaluates cloud provider permission models across identity, network, compute and data resources to surface precise findings in context. Gain comprehensive insight into identity-related risk, including excessive permissions, network exposure and hidden dangers.
根據您的需求自訂自動化修復
Tenable CIEM 可透過自動化與輔助式修復工具協助減輕有風險的權限和錯誤設定。Rapidly remove unintended entitlements and fix misconfigurations to eliminate the associated risk.
- Use wizards that display remediation steps and auto-remediation options
- 在現有的 DevOps 工作流程 (如 Jira 或 ServiceNow) 中插入自動產生的最佳化原則與設定修正
- 透過提供開發人員大小適當、最低權限的程式碼片段,縮短平均修復時間 (MTTR)
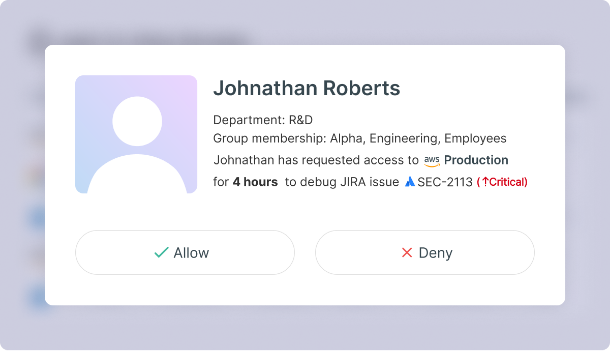
利用 Just-in-Time (JIT) 存取,在無需犧牲安全性的情況下提供創新的能力
您的工程團隊有時也會需要較高的特權來存取敏感的雲端環境,例如除錯或手動部署某項服務。Granting Broad access can introduce risk if not revoked when no longer needed. Tenable Just-in-Time (JIT) 存取管理功能可讓您根據業務判斷來控制開發人員的存取權限。With Tenable JIT you can enforce fine-grained least-privilege policies and avoid long-standing privileges, minimizing your cloud attack surface. 您可以讓開發人員快速地提交請求、通知核准者、並取得臨時存取權。您可以透過追蹤工作階段期間的活動及產生詳細的 JIT 存取報告來維持監管能力。
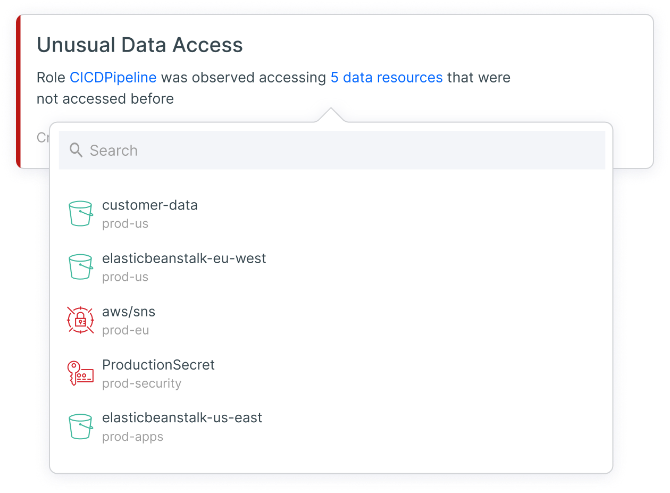
調查威脅與偵測異常狀況
利用 Tenable CIEM,您就可以對行為基準執行不間斷的雲端風險分析,以便偵測出異常狀況及可疑活動。Tenable CIEM 能判別以身分為目標的威脅,例如與資料存取相關的不尋常活動、網路存取管理、權限管理、特殊權限提升等等。透過查詢內容豐富的紀錄,您就能在背景資訊下瞭解、檢視並調查風險。You can further lower MTTR through integrations with SIEMs (such as Splunk and IBM QRadar) and with ticketing/notification systems (such as ServiceNow and Jira).
部落格:封鎖您的雲端影響範圍
持續的存取監管與合規
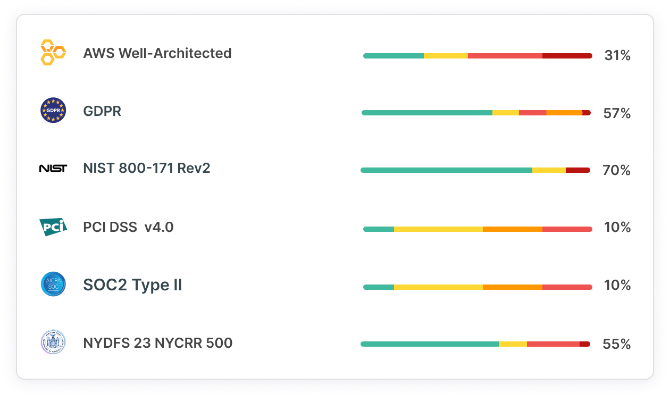
Security and privacy regulations such as CIS, SOC2 and HIPAA require organizations to have cloud security capabilities for governing access policy and enforcing least privilege. Effective controls enable continuous auditing and automated reporting on how you use privileged cloud identities. 您通往最低權限和提早執行安全性的途徑就從掌握所有權限完整與正確的面貌開始。Tenable CIEM analyzes how human and machine users access cloud resources and auto-generates access policies based on actual needs that integrate into your remediation workflows. Continuously verify compliance status and easily produce detailed reports.
深入瞭解:CSPM 解決方案
Tenable Cloud Security - 統一的 CNAPP
Tenable 可利用 Tenable Cloud Security 提供適用 AWS、Azure 和 GCP 的全方位雲端原生應用程式保護平台 (CNAPP)。 利用領先市場的雲端基礎架構與權限管理 (CIEM),您就能大幅減少雲端攻擊破綻並大規模強制執行最低權限原則。
深入瞭解 Tenable Cloud Security
“Using [Tenable Cloud Security] automation allowed us to eliminate exhaustive manual processes and perform in minutes what would have taken two or three security people months to accomplish.”
IntelyCare 資訊安全總監 Larry Viviano
- Tenable Cloud Security
 AWS
AWS Azure
Azure Google Cloud
Google Cloud