Tenable Identity Exposure secures active directory and eliminates attack paths
Tenable Identity Exposure secures active directory and eliminates attack paths
-
Decrease identity risk and secure human and machine identities with best practices for preventative Active Directory Security.
-
Unified view of identities across Active Directory and Entra ID (Formerly Azure Active Directory) deployments.
-
Enhance your ITDR (Identity Threat Detection and Response) capability by auditing Active Directory directory changes in real time and establishing timelines for indicators of attack.
-
Exposure management is based on calculated identity risk scores, focusing on areas of highest risk.
-
Continuous validations and assessment of AD for attack prevention and detection.
申請示範
Tenable customers - 65% of the Fortune 500 trust Tenable
With Tenable Identity Exposure, you'll always have:
Tenable Identity Exposure benefits
With Tenable Identity Exposure, you'll always have:

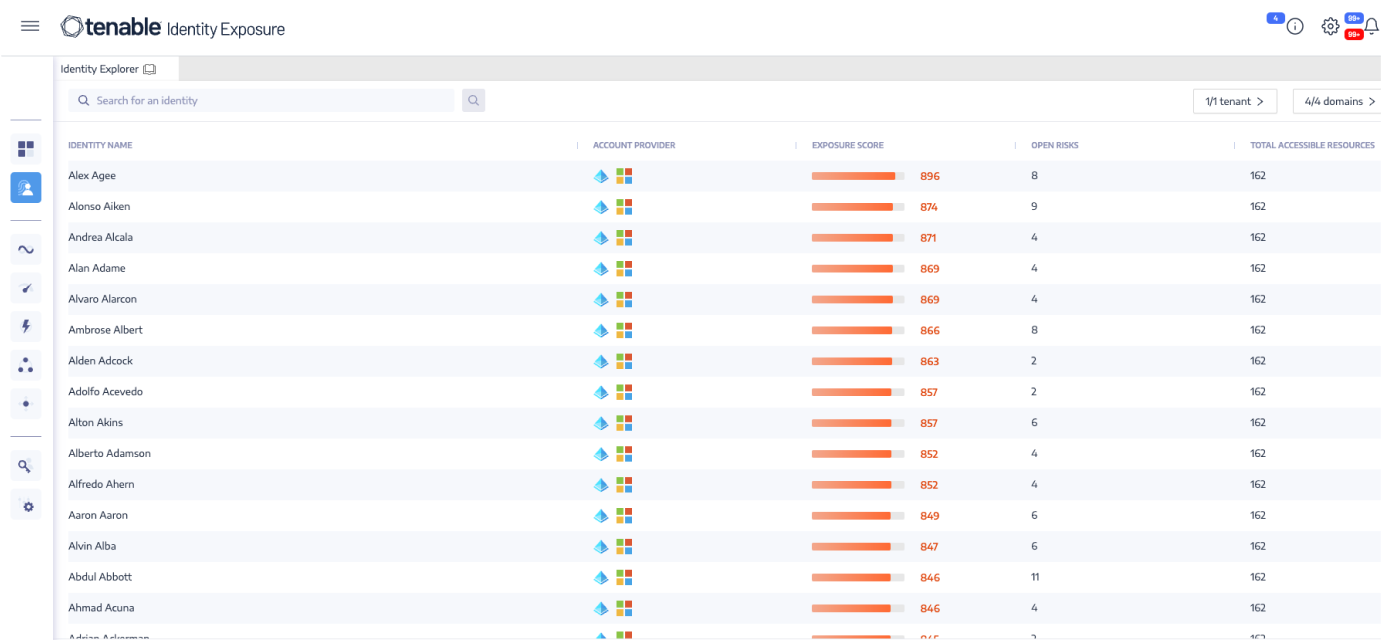
Identity unification and
AI-driven risk scoring
將 Active Directory、多元混合和 Entra ID 帳戶通通整合成單一檢視畫面。Gain control of identities dispersed between multiple directory services, domains and forests in a single view. Prioritize remediation with our data-science backed identity risk score that ranks identities by level of risk to the environment. Optimize team efficiency and focus efforts on risk mitigation and preventing attacks.
Expand
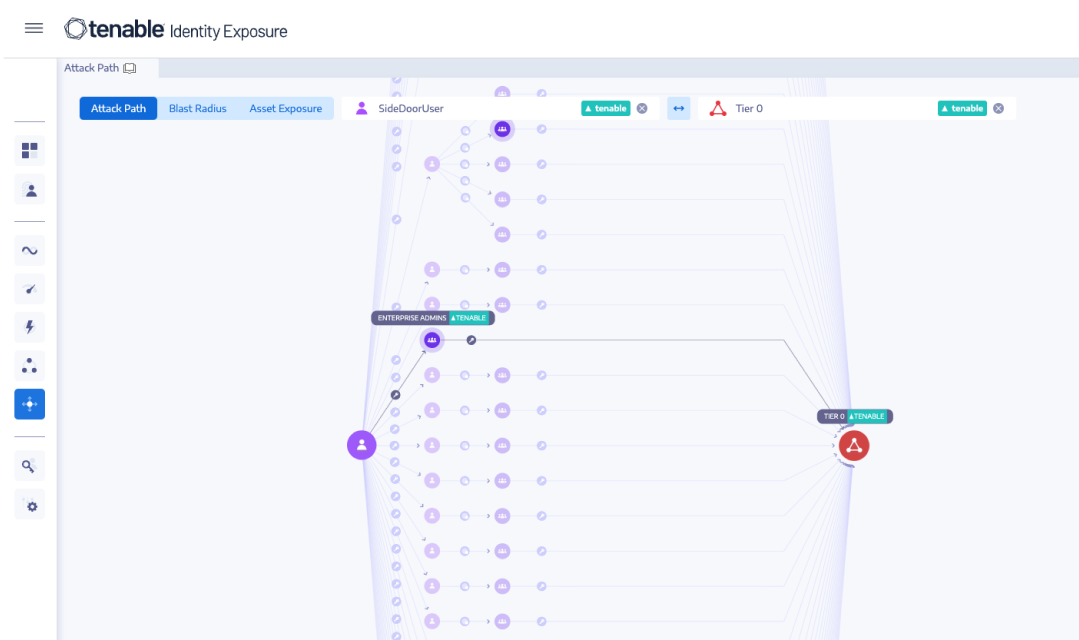
Eliminate attack paths that lead to domain domination
Make sense of the complex interrelationships between objects, principals, and permissions, and eliminate attack paths that lead to domain dominance. Attack path analysis surfaces all the possible steps that attackers could take to move laterally, escalate privileges, and gain control over your enterprise directory services.
Expand
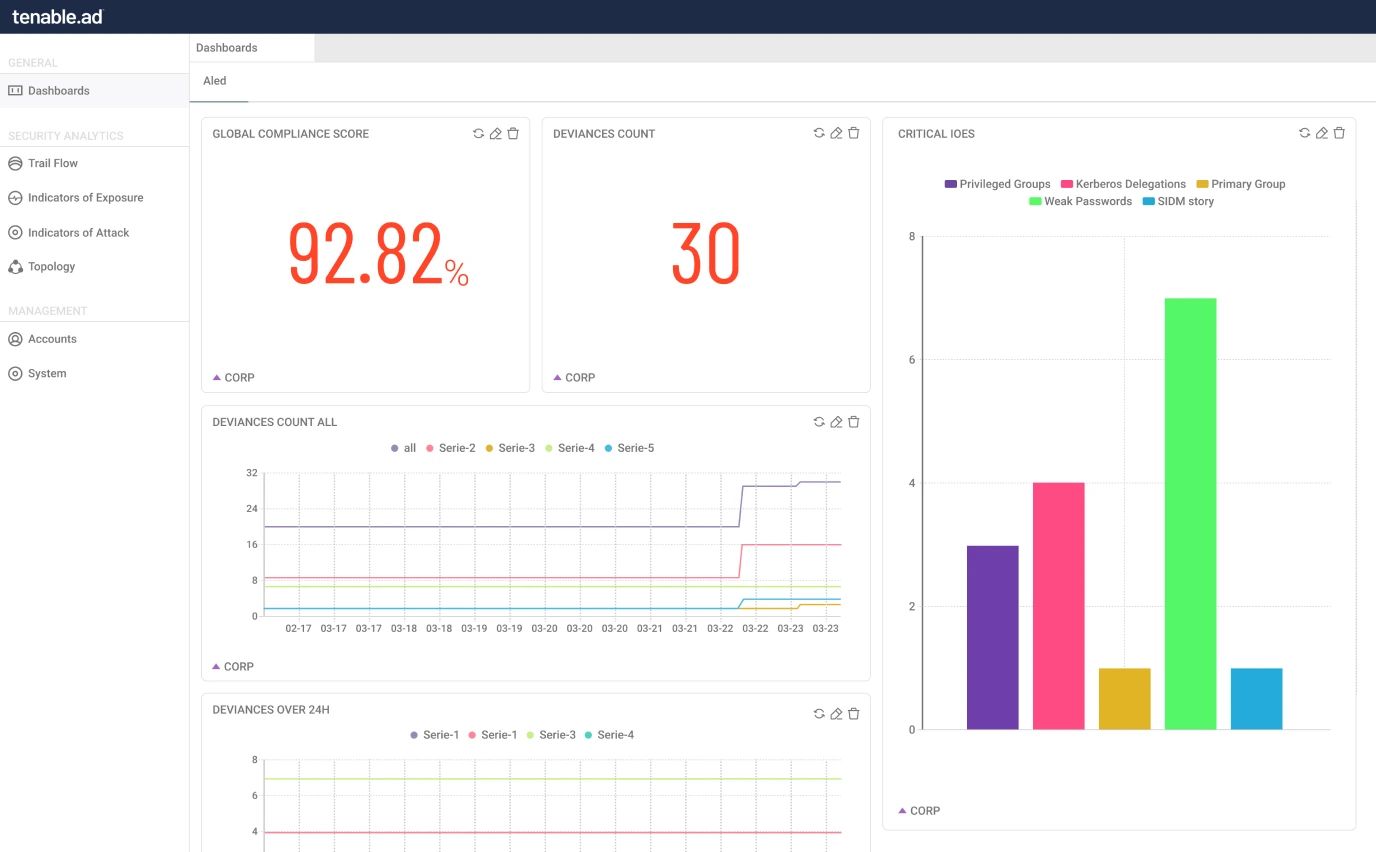
Continually assess directory services security in real-time
評估企業目錄服務的安全態勢並找出弱點、有風險的設定和權限蔓延問題。Tenable Identity Exposure provides a step-by-step tactical guide that identifies affected objects, eliminating the need for time-consuming manual reports or scripts, hardening AD and Entra ID.
Expand
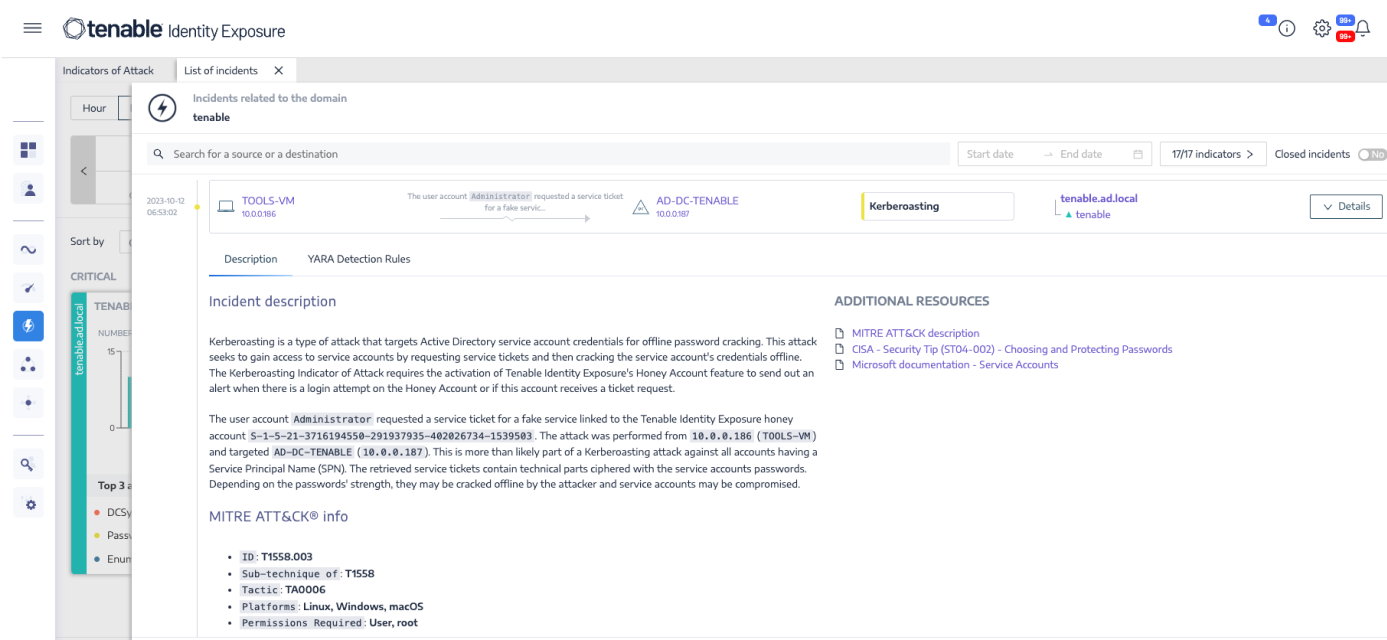
Real-time attack detection
Receive instant alerting against indicators of attack, including credential dumping, Kerberoasting, DCSync, ZeroLogon, and many more. Respond to attacks in real time by integrating Tenable Identity Exposure with your SIEM and SOAR. Tenable’s research team regularly updates indicators of attack as new identity-based exploits are discovered.
Expand
Investigate and inform
Reduce MTTR (mean time to respond) and audit active directory by capturing all changes to Active Directory using Trail Flow. Inform your incident response teams and enrich your security operations processes with real-time prioritization and detailed remediation steps.
Expand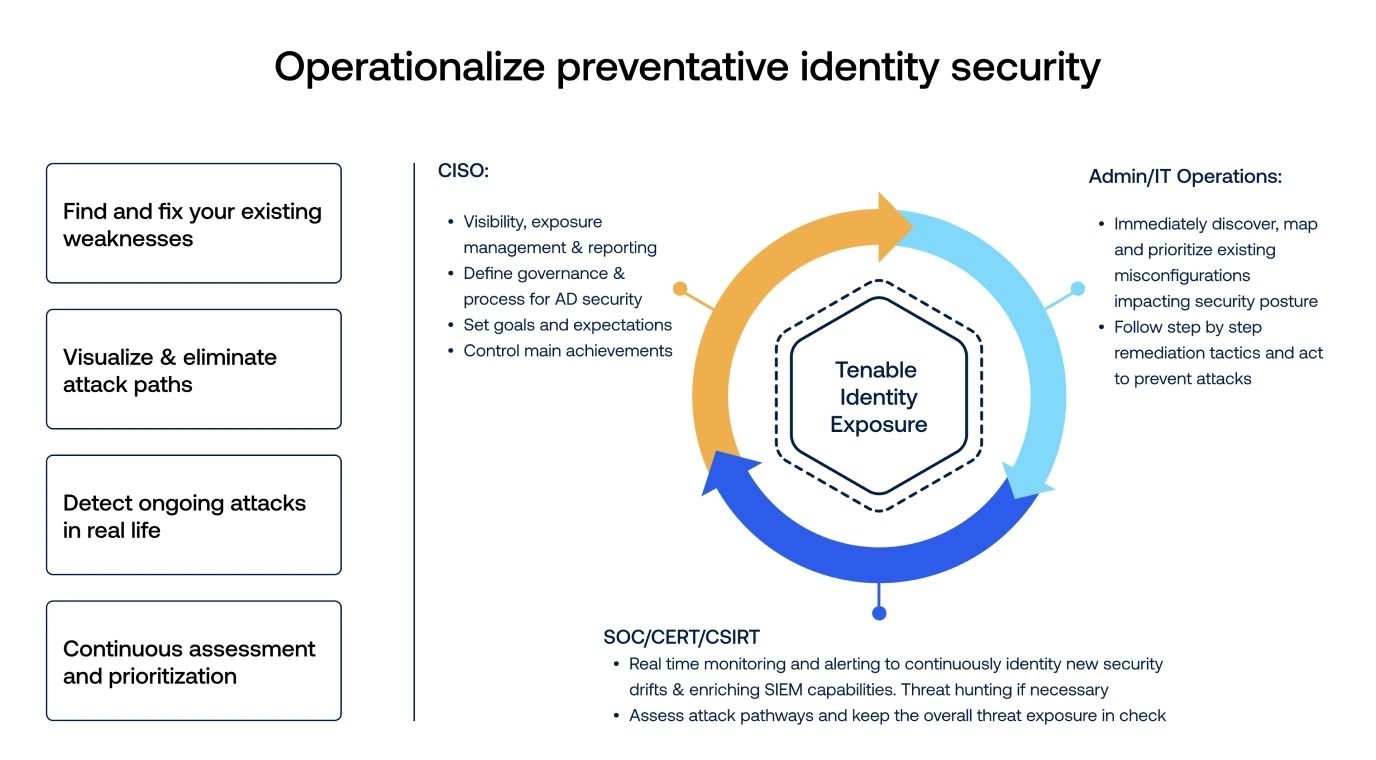
Introduction to Tenable Identity Exposure and Identity Aware Exposure Management
A quick walkthrough of Tenable Identity Exposure highlighting why Identity aware exposure management provides critical context to prioritize cyber security remediation efforts.
Continuously detect
and prevent active directory attacks
-
無需代理程式、No privileges.
沒有延遲無需代理程式和特殊權限,就能防止並偵測複雜的 Active Directory 攻擊。
-
Clouds covered
Extended support for protecting public and hybrid cloud Azure Active Directory deployments and managing cloud identity risk with Indicators of Exposure specific to Azure AD.
-
在任何地點部署
Tenable Identity Exposure 提供了兩種架構設計的彈性。 內部部署能讓您將資料保留在現場,並且在您的控制之下。軟體即服務 (SaaS) 則能讓您運用雲端。