by David Schwalenberg
May 18, 2017
Optimal network security requires more than just preventative measures. Without monitoring configuration compliance, misconfigured devices could allow actions that put critical systems and sensitive data at risk. Without continuously monitoring network activity, unusual activity that could be dangerous or malicious in nature might never be seen. The financial industry is highly targeted by cyber attacks, emphasizing the urgent need for robust cyber security and increased network resilience.
In 2016, due to the increasing use of information technology by banks and their customers, and the increase in cyber attacks against the financial sector, the Reserve Bank of India (RBI) provided guidelines in the area of cyber security to banks. The guidelines document, Cyber Security Framework in Banks, includes an Annex detailing minimum baseline requirements for network security and resilience. These requirements cover such areas as inventory management, secure configuration, patch management, access control and advanced real-time threat defense.
Tenable's Tenable.sc Continuous View® (Tenable.sc CV™) offers several specialized dashboards that can help banks comply with the requirements specified in the RBI document. This dashboard assists in the area of continuous network monitoring, and aligns with paragraph 12 ("Banks need to take effective measures ... to promptly detect any cyber-intrusions...") of the RBI document, as well as the following baseline controls in Annex 1:
- 4 (Network Management and Security)
- 5 (Secure Configuration)
- 8 (User Access Control/Management)
- 12 (Removable Media)
- 13 (Advanced Real-time Threat Defence and Management)
- 15 (Data Leak Prevention Strategy)
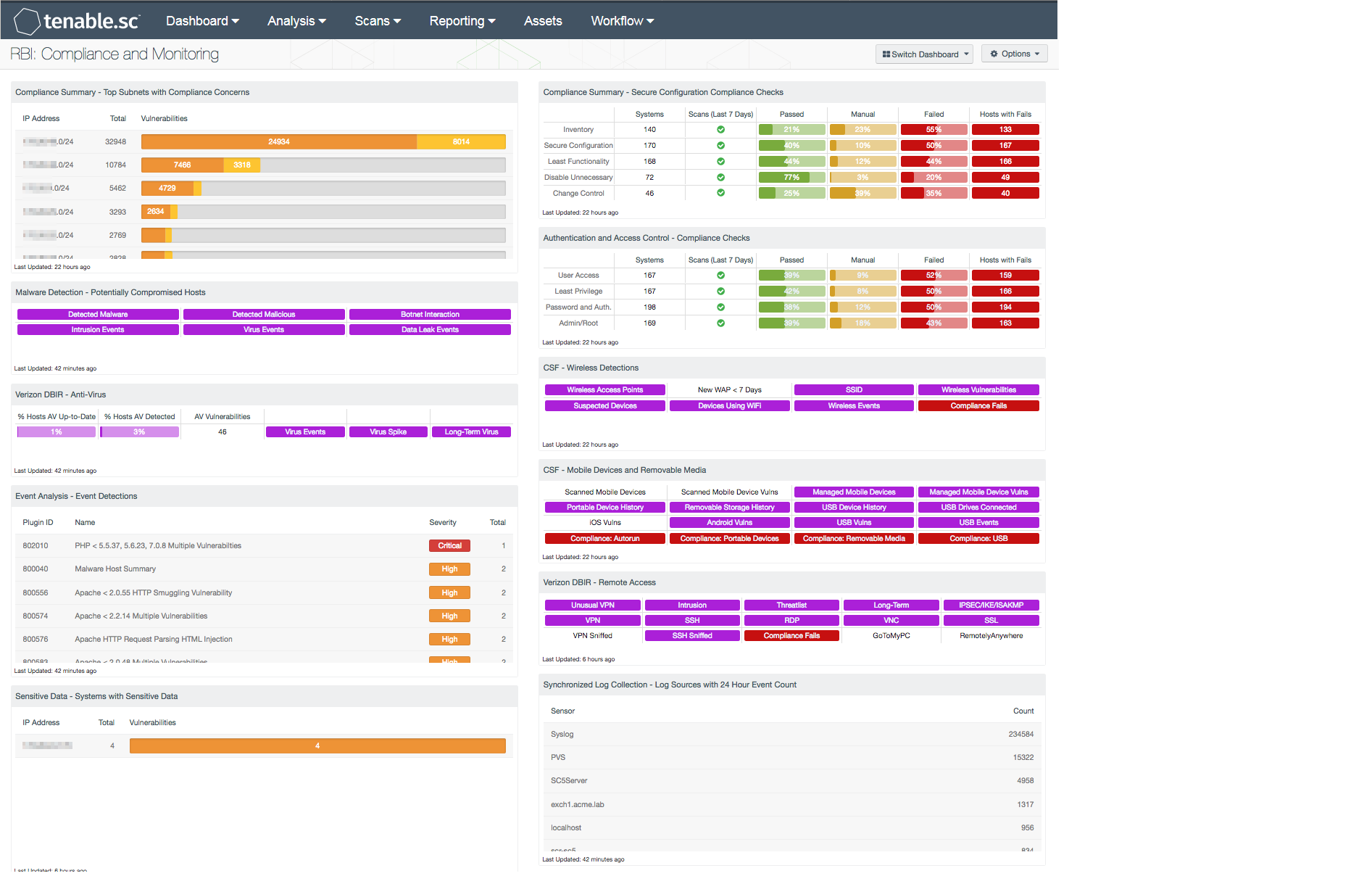
For compliance monitoring, this dashboard presents the results of audit scans in areas such as secure configuration and access control. Compliance failures in the areas of wireless, mobile devices, removable media and remote access are also indicated. Compliance concerns totaled per subnet give the organization a sense of where to focus compliance efforts.
This dashboard also presents indicators of potentially compromised hosts, such as detections of malware installed on hosts and hosts with suspicious communications to known botnets. This information can help organizations detect and deal with cyber attacks. The anti-virus status of devices on the network is summarized, allowing the organization to monitor their anti-virus protection. Event detection, as well as detection of wireless, mobile devices, removable media and remote access, assists the organization in monitoring for any unusual activity that might indicate a cyber attack.
In addition, systems that appear to contain sensitive data, based on a file contents audit, are noted. A file contents audit looks for keywords and patterns (such as credit card numbers) in the first several kilobytes of a file to determine if the file contains potentially sensitive data. This information enables the organization to determine whether sensitive data is not encrypted and possibly in the wrong place.
The information on this dashboard helps the organization to lock down and monitor configurations, and to detect potentially malicious activity, as specified in the RBI requirements. This continuous monitoring in turn allows cyber attacks to be caught early, before serious damage to systems and data can be done.
This dashboard is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment. The dashboard requirements are:
- Tenable.sc 5.4.5
- Nessus 8.5.1
- LCE 6.0.0
- NNM 5.9.0
- Compliance data
Tenable's Tenable.sc CV is the market-defining continuous network monitoring solution, and assists in securing an organization’s internal network. Tenable.sc CV is continuously updated with information about advanced threats, zero-day vulnerabilities and new regulatory compliance data. Active scanning periodically examines systems to detect vulnerabilities and compliance concerns on network assets. Passive listening provides real-time detection of assets and discovery of vulnerabilities. Host data and data from other security products is analyzed to monitor the network for malware, intrusions and other forms of malicious activity. Tenable.sc CV provides the organization with the most comprehensive view of the network and the intelligence needed to support proactive continuous monitoring efforts.
The following components are included in this dashboard:
- Compliance Summary - Top Subnets With Compliance Concerns: This table presents the top Class C subnets with the most compliance concerns.
- Malware Detection - Potentially Compromised Hosts: This component presents indicators that highlight potentially compromised hosts.
- Verizon DBIR - Anti-Virus: This matrix assists the organization in monitoring anti-virus solutions.
- Event Analysis - Event Detections: This table presents all detections from event plugins associated with the Tenable Log Correlation Engine (LCE).
- Sensitive Data - Systems With Sensitive Data: This component presents a summary of systems with files that contain sensitive data.
- Compliance Summary - Secure Configuration Compliance Checks: This component presents the results of compliance audits to verify the secure configuration of systems, including least functionality, disabling unnecessary services and inventory and change control settings.
- Authentication and Access Control - Compliance Checks: This component displays compliance information in the areas of user access, least privilege, password and authentication requirements, and administrative/root account control.
- CSF - Wireless Detections: This component presents a breakdown of detected wireless access points, wireless vulnerabilities and wireless event activity on the network.
- CSF - Mobile Devices and Removable Media: This component assists an organization in monitoring mobile devices and removable media.
- Verizon DBIR - Remote Access: This component assists an organization in monitoring remote access to systems.
- Synchronized Log Collection - Log Sources With 24 Hours Event Count: This component identifies log sources and helps the organization ensure that all systems that can send logs are sending them to LCE and/or allowing NNM to scan them.